Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove MOTD Ransomware?
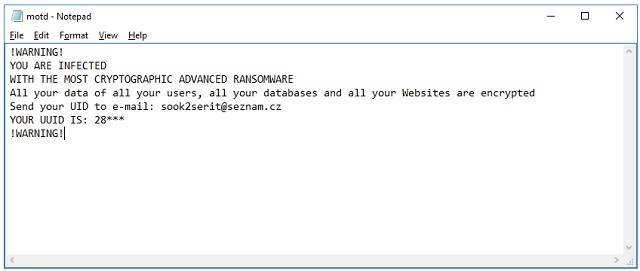
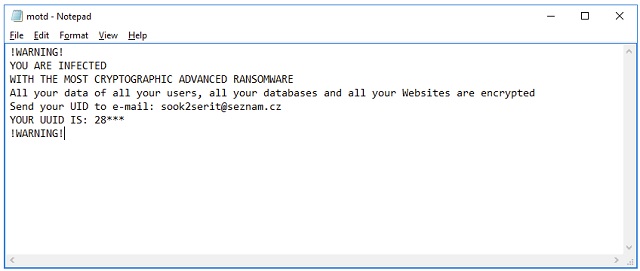
Readers recently started to report the following message being displayed when they boot their computer:
!WARNING!
YOU ARE INFECTED
WITH THE MOST CRYPTOGRAPHIC ADVANCED RANSOMWARE
All your data of all your users, all your databases and all your Websites are encrypted
Send your UID to e-mail: sook2serit@seznam.cz
YOUR UUID IS: 28***
!WARNING!
The MOTD Ransomware is a complete pest. This program belongs to one notoriously dangerous type of infections. There is a reason why ransomware is so dreaded. You’re now stuck with a file-encrypting virus which locks your private files. All your files. As if that wasn’t bad enough, ransomware demands money in exchange for a decryption key. Do you see the scam already? As soon as you come across the MOTD Ransomware, you have to take action. You will find all the information you need about this program in today’s article. In addition, we’ve prepared a detailed removal guide down below. Now, how does the virus work? It gets to work immediately after installation. Needless to say, the installation itself happens in silence. Nobody would download a vicious file-encrypting virus on purpose. The problem is, you may spend a good while having no clue MOTD Ransomware is on board. This infection will use all this time to wreak havoc. It performs a thorough scan on your machine. By doing so, MOTD Ransomware finds all your private data. That includes photos and music and videos and presentations and documents. Ransomware works with a huge variety of formats. Its shenanigans will inevitably cause you a headache unless you keep backup copies. In the future, always make sure you have backups of your data. After all, your data is what ransomware is aiming at. To protect yourself from damage, you should think in advance. The MOTD Ransomware uses RSA ciphers to encrypt your files. As mentioned, all your precious files fall victims to the parasite. Once your data gets encrypted, you’ll notice an .enc file extension. This is a crystal clear sign that your information is locked. You see, ransomware modifies the format of your files. It turns them into unreadable gibberish and denies you access to your own data. Think about it. Hackers encrypt your information and make it unusable. Then they have the impudence to ask for a ransom. While locking your files, MOTD Ransomware adds a motd.txt tile. That’s your ransom message. You will find these notes in all folders that contain locked information. It goes without saying that those are indeed a lot of folders. The virus might also alter your desktop wallpaper too. According to all these ransom notes, you must make a payment in order to free your data. Are you willing to give money to the very people who caused you all of this? Keep your Bitcoins and delete the ransomware ASAP.
How did I get infected with?
Just like all other ransomware infections, this one uses stealth. The most preferred tactic includes spam emails. If you receive something suspicious in your inbox, you should stay away from it. Clicking a corrupted email open is all it takes for a virus to get installed. Crooks rely on your distraction as well as curiosity. To prevent malware infiltration, always keep an eye out for potential threats. The Web is infested with parasites. Now that you’ve witnessed the tricks ransomware is capable of, why underestimate the danger? Put your security first. You won’t regret it. Delete the random email-attachments and messages you don’t trust. Clicking them open unless you personally know the sender could be a mistake. And you can’t afford any mistakes when surfing the Web. Be careful when installing software too. Restrain yourself from downloading illegitimate programs, especially when they are bundled. You might give green light to some nasty infection without even knowing it. Ransomware gets spread online via fake program updates, bogus torrents, corrupted third-party ads, exploit kits, etc. Protecting your computer isn’t a particularly challenging task. You just have to be more careful and attentive when browsing the Internet.
Why is MOTD dangerous?
You’re supposed to pay in order to free your files. Does that really seem like a fair deal to you? Hackers are the ones who put you in this position. Should they be rewarded for their tricks and lies? Don’t be gullible. Even though the parasite’s ransom notes promise a decryptor, this is yet another lie. All that cyber criminals are interested in is stealing your Bitcoins. Therefore, giving into your anxiety will cost you money. The ransom instructions provide you an email address – sook2serit@seznam.cz. Using it would contact you straight with hackers so keep that in mind. Do not pay anything because that’s how you fall in crooks’ trap. To delete the ransomware manually, please follow our comprehensive removal guide.
MOTD Removal Instructions
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover MOTD Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.
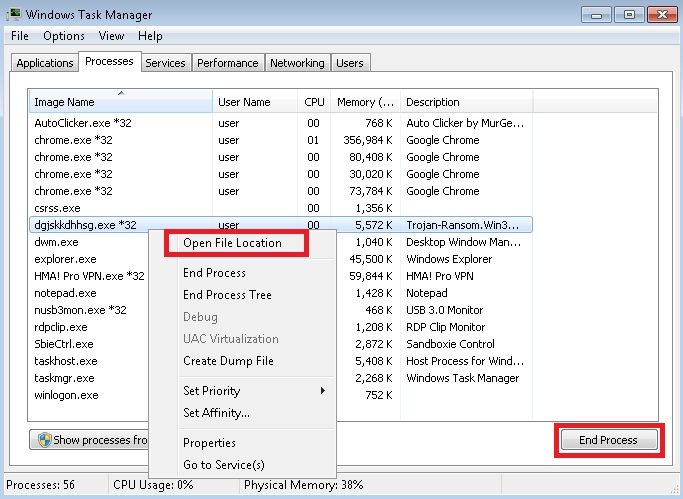
- Locate any suspicious processes associated with MOTD encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate MOTD encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]
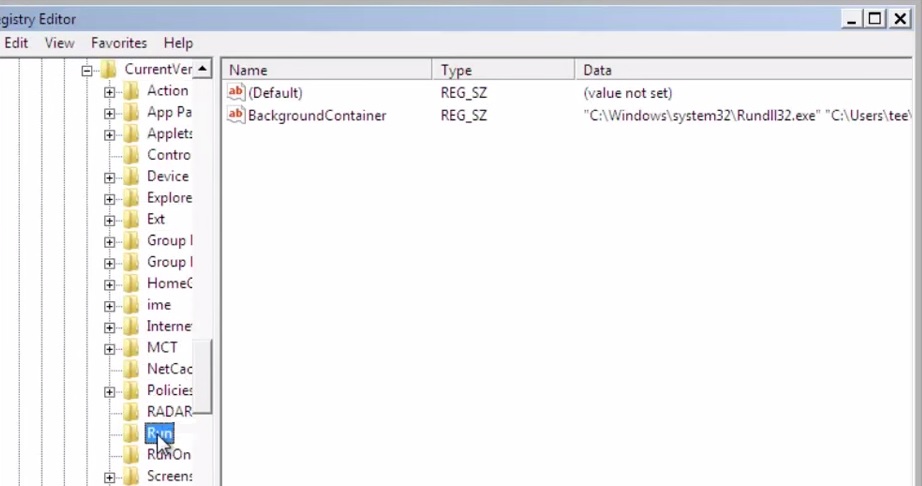
- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
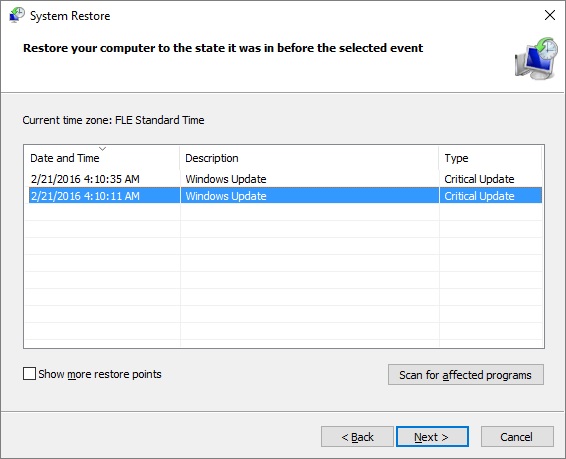
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.
- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.