Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove PetrWrap Ransomware?
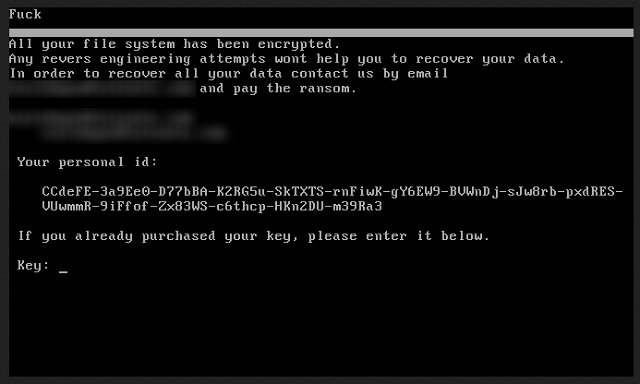
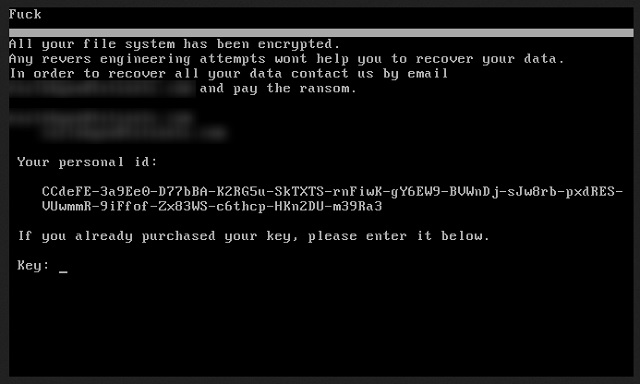
Readers recently started to report the following message being displayed when they boot their computer:
F**c
All your file system has been encrypted.
Any revers engineering attempts wont help you to recover your data.
PetrWrap is a new player on the ransomware board. It’s a newly discovered threat that belongs to that category of infections. But, even though, it seems to be a new menace, it’s rather an old one with a twist. Let’s elaborate. Do you remember the Petya infection? It’s a dreadful ransomware that lead to the creation of dozens of ‘sister’ threats. Mischa, Kostya, !SATANA!, et cetera. They all derive from the parent program, Petya. PetrWrap is its latest offspring. But, it differs from the rest. It does not profit Petya’s makers. Let’s get into it, cause it’s a bit confusing. The PetrWrap tool is a modified version of Petya that has different creators. The cyber criminals behind PetrWrap have changed the initial code. It varies in a way that leaves all revenue in their possession. So, it’s untouchable by the original infection’s architects. The new founders replaced Petya’s ECDH algorithm with a different one. That way, the PetrWrap designers could generate private and public keys outside the RaaS system. That whole process is known as “wrapping.” Hence, the ransomware’s name – PetrWrap. The criminals behind Petya can do nothing against these ‘innovators.’ And, do you know what? Neither can you after the tool strikes. The PetrWrap ransomware is a plague on your system. One, you cannot fight. It takes over, backs you into a corner, and demands compliance. Don’t grant it. Whatever move you make, you will lose. The game is rigged against you from the start. The best thing you can do is choose not to play. So, when the program takes over your files, let it have them. Discard your data. It’s the safest alternative, compared to the rest.
How did I get infected with?
PetrWrap turns to the usual antics to gain entry to your system. It uses the old but gold methods to invade your PC. But, here’s the thing. The tool cannot succeed in its invasive tactics without one key ingredient. Your carelessness. If you are vigilant and thorough, you improve your odds of having an infection-free PC. That’s why due diligence is imperative. But if you go the opposite direction, brace yourself. Distraction, naivety, and haste tend to lead to cyber threats. The common methods include freeware and spam email attachments. As well as corrupted links, and bogus updates. For example, you may believe you’re updating your Java, but you’re not. In actuality, you’re going through with the install of a dangerous cyber plague. Here’s where vigilance comes in quite handy. If you’re attentive enough to catch the tool in the act, you can prevent its admission. If you’re not, you reap the ‘rewards’ shortly. Choose caution over carelessness. Oftentimes, even a little extra attention goes a long, long way.
Why is PetrWrap dangerous?
PetrWrap’s design when it comes to encryption is rather standard. The too doesn’t stand out with originality. After it sneaks into your system, its programming kicks in. The tool takes over your system. It locks every single file you keep on your computer. It adds a special extension at the end of each file, thus solidifying its grip. When your data gets locked, the tool displays a ransom note. It contains basic information. It explains your predicament, and gives you a way out. In a nutshell, if you wish to decrypt your files, pay a ransom. Upon completion of payment, you’ll receive a special key that decrypts your data. That sounds pretty straightforward, right? Well, wrong. Remember that you’ll rest on cyber criminal’s ability to keep their word. Can you trust them to go through with their promise? Here’s your answer: No. Don’t fool yourself. Don’t be naive. These are cyber extortionists. People, who unleashed a dreaded program onto unsuspecting users. All in the hopes of making a profit. Don’t hold your breath over their reliability. Even if you comply with their demands to your fullest, odds are, you lose. Think about it. What are your options? You pay, and they send you a decryption key. But what if they don’t? Or, what if they give you the wrong one? And, even if it’s the right one, don’t rejoice. The decryption key remove the encryption over your data. It does not remove the infection itself. So, the PetrWrap program remains. What’s stopping it from acting up again? Nothing. The tool’s programming can kick in moments after decryption. Hours, days, weeks. The point is, it’s still there, on your computer, ready to send you back to square one. Only this time, you’ll have less money. And, what’s worse, an exposed private life. Oh, yes. Let that sink in. When you transfer the money, in exchange for the decryption key, you provide private details. Personal and financial information. When you do that, the cyber kidnappers behind PetrWrap, then have access to it. They can use that information as they see fit. Do you think that ends well for you? Is that a chance you’re willing to take? Or, would you rather minimize your losses, and choose to forsake your files. It’s a tough choice to make, but it’s the right one. Let go of your pictures, documents, music, videos, and so on. Keep your private life private. After all, files are replaceable. Privacy is not.
PetrWrap Removal Instructions
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover PetrWrap Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.
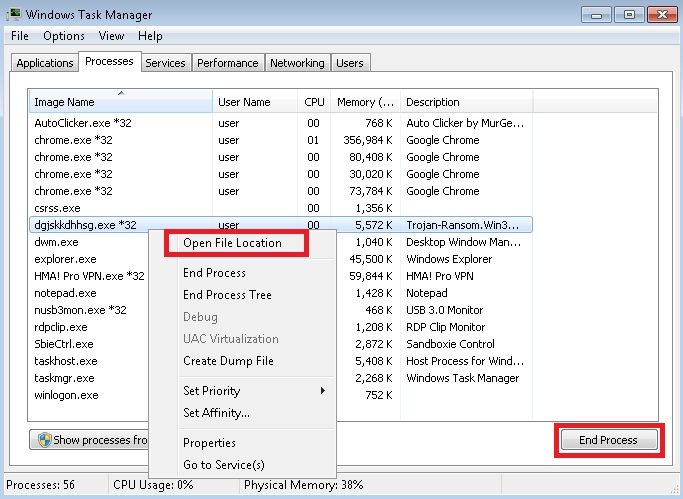
- Locate any suspicious processes associated with PetrWrap encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate PetrWrap encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]
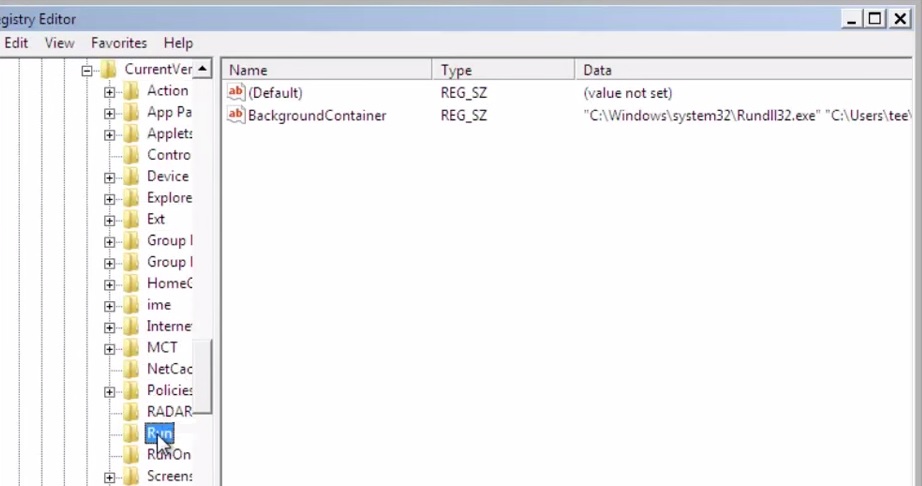
- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
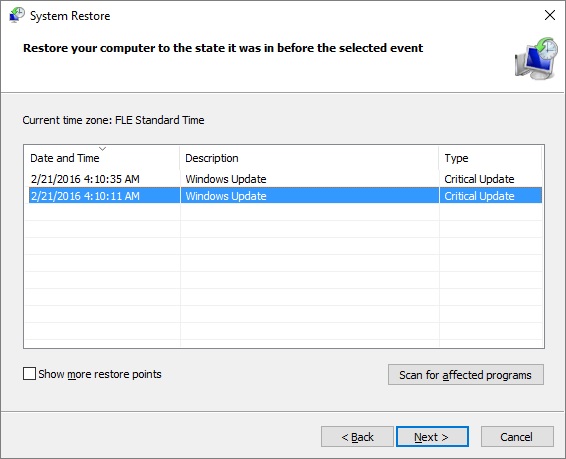
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.
- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.