Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Popcorn Time Ransomware?
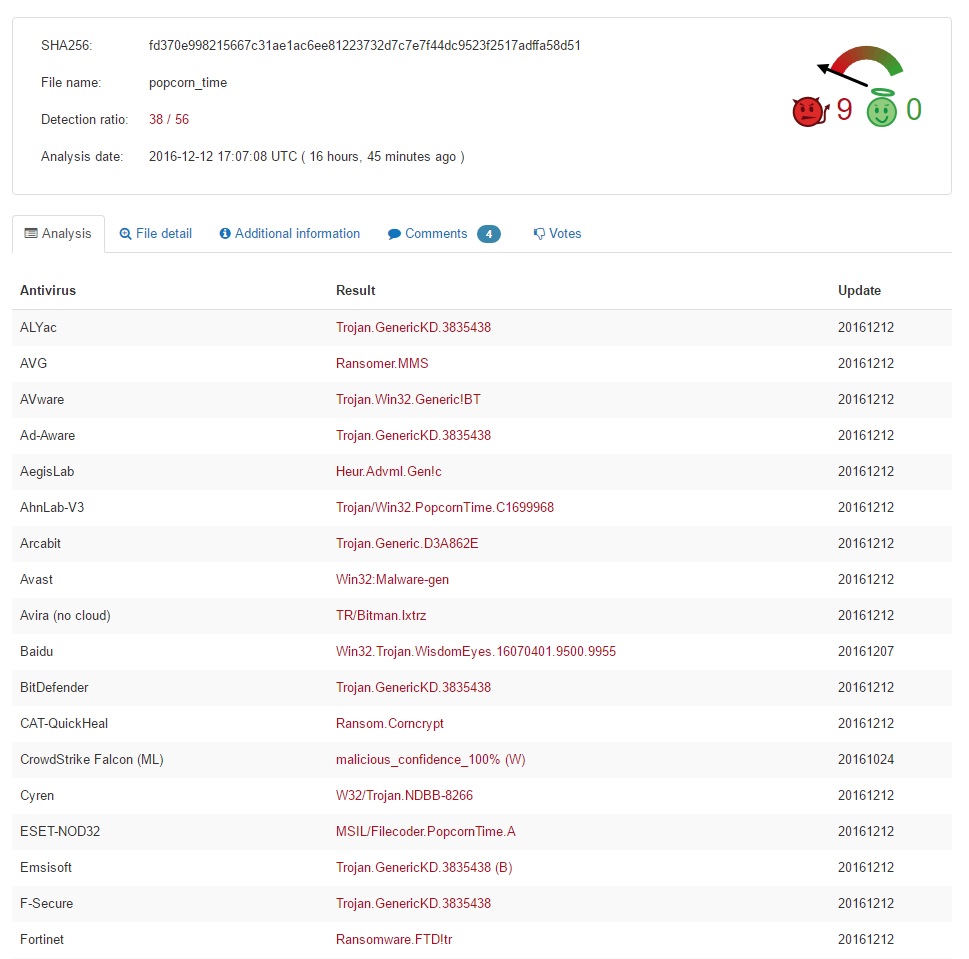
Popcorn Time doesn’t sound particularly frightening, does it? You’re in for a very bad surprise, though. Note the Popcorn Time Virus has nothing to do with the harmless tool that allows you to watch movies. No. Thanks to hackers’ tireless efforts, this name is now associated with a cyber infection. Furthermore, Popcorn Time is quite unique. Not only does this pest encrypt your files but it also directly asks you to spread the virus. Popcorn Time offers you a choice – you either pay a certain sum of money or infect two people. To say the least, this is one unusual tactic. We have never come across a ransomware program that uses such a nasty trick. As soon as the parasite gets downloaded, it scans your computer system. The virus searches for one specific file named been_here. If said file is present, that means your PC has already been infected with the ransomware. In this rare scenario, the parasite deletes itself. Otherwise, it initiates encryption process. There is a reason why ransomware-type viruses are so immensely dreaded. These programs lock your personal files. Every single bit of information stored on your machine gets encrypted. Pictures, music, MS Office documents, videos, etc. Popcorn Time effectively encrypts a huge variety of formats. It uses the strong AES-256 encryption algorithm and adds a malicious appendix. Seeing the random .filock extension means it is game over. For example, IlovePopcorn.mp4 gets renamed to IlovePopcorn.mp4.filock. As you could imagine, your data gets renamed completely behind your back. Hackers rely on the element of surprise. Many people would panic when they see such sudden, unauthorized modifications. Not to mention, locking your files could cause you some serious damage. The infection denies you access to your own files which might be incredibly important. Private pictures. Work-related documents. Your favorite music files. Popcorn Time takes down all your information. It also creates restore_your_files.html and restore_your_files.txt files. Your desktop wallpaper is modified as well so you’re constantly seeing ransom notes. The ransom message displayed by Popcorn Time is extraordinary. As mentioned, hackers offer you a way to free your data without paying. Unfortunately, it includes spreading the parasite. According to the ransom notes, you must infect two people with the ransomware. Then you’re supposed to receive a decryption key in order to restore your encrypted data. Needless to say, this is just a cheap trick and a lie.
How did I get infected with?
The easiest infiltration technique involves spam emails. That means next time you receive some questionable email, you have to delete it. Crooks could send all kinds of dangerous, corrupted emails straight to your inbox. Be careful not to click any of them open. Preventing infiltration is much easier than deleting some vicious cyber virus afterwards. Keep that in mind and be careful when surfing the Internet. You might stumble across some devastating infections and compromise your PC without even knowing it. Ransomware also travels the Web via exploit kits, illegitimate websites, corrupted program updates, etc. Your caution will pay off in the long run. Stay away from third-party pop-ups too. Last but not least, these programs also use the help of Trojan horses. Check out the entire computer for more infections. The Popcorn Time Ransomware might be having company on board. Now that you know how destructive it is, are you willing to deal with ransomware again? Make sure you protect your security and privacy. You certainly won’t regret it.
Why is Popcorn Time dangerous?
The Popcorn Time Virus is aggressive, stealthy, dangerous and unpredictable. Quite a combination, isn’t it? This is a relatively new infection. It is still within development so hackers could make it even more troublesome. Popcorn Time also threatens you with DELETING your files. The sum crooks demand is 1.0 Bitcoin which equals almost 780 USD. What’s even worse is that you’ll receive absolutely nothing in exchange for your Bitcoins. Ransomware is a clever attempt for a cyber fraud so you can’t afford a single wrong move. Don’t even consider contacting cyber criminals because your encrypted data is their last concern. Even though they promise you a decryptor, it’s hackers we’re talking about. To say the least, they aren’t famous for being honorable people. Popcorn Time is trying to trick you into either paying a ransom or spreading the virus online. Both options do not guarantee you any decryption key whatsoever. To delete this nuisance manually, please follow our detailed removal guide down below.
Popcorn Time Removal Instructions
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Popcorn Time Encrypted Files
WARNING! Stopping the wrong file or deleting the wrong registry key may damage your system irreversibly.
If you are feeling not technical enough you may use Spyhunter professional Popcorn Time Removal Tool. However, only the Scanner is FREE, in order to remove the Popcorn Time virus completely you need to purchase full version. >>Download SpyHunter – a professional Popcorn Time scanner and remover.
>>Download SpyHunter – a professional Popcorn Time scanner and remover.
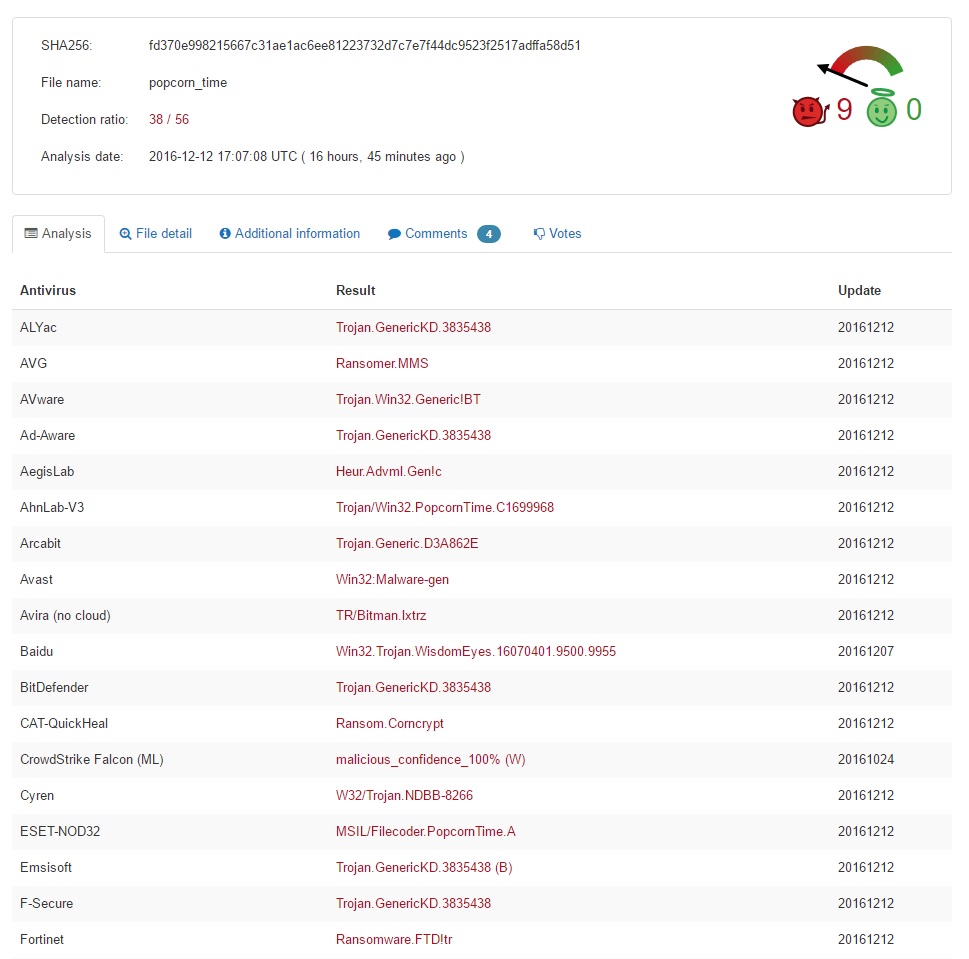
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.
- Locate any suspicious processes associated with Popcorn Time encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
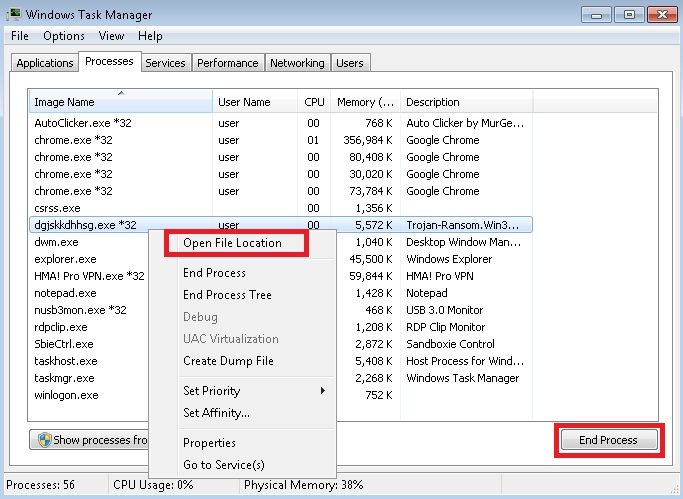
STEP 3: Locate Popcorn Time encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]
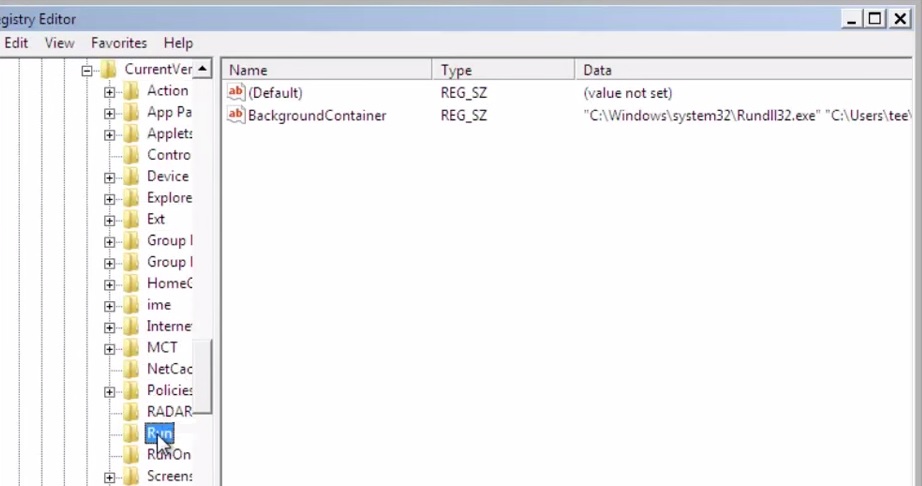
- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
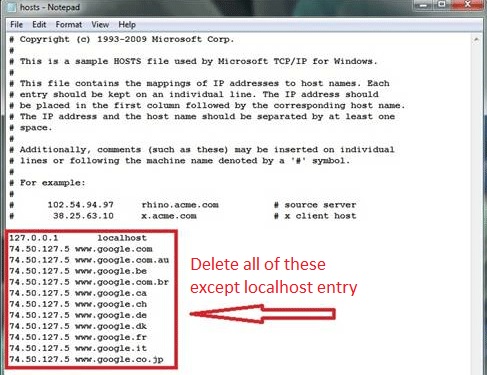
Navigate to %windir%/system32/Drivers/etc/host
If you are hacked, there will be foreign IPs addresses connected to you at the bottom. Take a look below:
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.
- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.