Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Amagnus@india.com Ransomware?
The ‘india’ line of ransomware tools keeps growing in numbers. There are more and more programs of the type popping up. They all follow the same pattern, and cause the same mess. The latest one is associated with the Amagnus@india.com email. The infection, attached to the address, is a variant of the Dharma ransomware. And, the Dharma too, in turn, was a variant of the Crysis infection. Now that you’re caught up with the lineage of the Amagnus tool, here’s how it works. The program invades your PC, and then corrupts it. It’s a simple principle. The ransomware encrypts all your data, and extorts you for money. After it’s done with the encryption process, it displays a ransom note. It’s in every folder, containing encrypted data. And, it’s on your Desktop, as well. It shows you basic information. The note explains your predicament, and what you’re expected to do. If you want to unlock your files, you have to comply with its demands. Supposedly, you pay up and, then, receive a decryption key. Apply it, and your files are free. But. Here’s the thing. What if it doesn’t send you one? Or, sends you the wrong one? Or, it’s the right one and it works, but two hours later, your data gets locked again? After all, the decryption key removes the encryption, not the infection. The Amagnus ransomware still remains on your PC, ready to strike once more. Understand this. When it comes to ransomware, all ransomware, there are no guarantees. The only thing that’s pretty much guaranteed, is that the tool WILL double-cross you. Ransomware tools are NOT to be trusted! The Amagnus infection is no different! It’s a cyber plague. And, you have to do your best to contain its damages. Limit them to your data only. Don’t let the nastiness spread! If you comply, you threaten your privacy. So, don’t! Protect your private life by forsaking your files. It’s a tough choice to make. But it’s the right one.
How did I get infected with?
Ransomware programs use deception to slither in undetected. And, you have no idea of their presence on your PC. Not until the tool takes over, and encrypts everything. But how do you suppose it manages to sneak past you? Well, ransomware applications rely on slyness and subtlety. They turn to the old but gold methods of invasion. The most preferred of which is spam email attachments. The programs hide behind legitimate-looking emails. If all of a sudden, you find an email by an unknown sender, be wary! Malware tends to disguise itself as an attachment. If you download it, that’s it. You allow the infection into your system, and you don’t even know it. So, if you see an email sent by PayPal, double-check if it’s from the real company. The best advice to follow is to not open any email you deem suspicious. And, if you open one, do NOT download attachments or open links, found in it. They’re trouble. Other ways, the Amagnus tool can use to slither in include freeware and fake updates. If you wish to keep such nasty programs away from your system, be cautious! Cyber threats prey on carelessness. So, be twice as vigilant when installing tools or updates. Even a little extra attention today can save you a ton of issues tomorrow.

Why is Amagnus@india.com dangerous?
So, what happens after the ransomware sneaks into your PC undetected? Well, you might get lucky and have a few days of bliss. A few days of the ransomware laying low, and NOT kicking in. But, that kind of luck is unlikely. What is likely, is that its programming sets off immediately after infiltration. Then, you discover the mistake you’d made. All of a sudden, the consequences of your carelessness become quite apparent. Every single file you keep on your computer gets locked. You find each one with a newly added extension. And, no matter how many times you change the name back, the file remains locked. Once the Amagnus tool appends the extension, that’s it. Your data is no longer accessible. The only way to decrypt what got encrypted is with a special key. And, as you’ve probably guessed by now, it costs you. Half a Bitcoin, one full Bitcoin, sometimes even much more than that. And, since 1 Bitcoin equals about $600, it’s no chump change. What you have to understand that even if the tool wanted a single dollar from you, you still shouldn’t pay. Why? Well, because it’s a trap. If you fall for it, you’re in so deep, there’s no escape. Let’s explain. To pay the cyber kidnappers, you contact them via the Amagnus@india.com email. Then, they provide you with more extensive information on payment. And, think about it. To do that, you have to provide personal and financial details. Then, courtesy of the magic of keyloggers, the cyber criminals get their hands on it. They get access to your private data. And, once they do, they can use it as they see fit. And, no pictures, documents and whatnot, are worth that risk! That’s why experts advise towards NOT complying! Do NOT pay the ransom. Discard your data in the name of your privacy. One is clearly much more important than the other. Figure out your priorities, and act accordingly.
Amagnus@india.com Removal Instructions
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Amagnus@india.com Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.
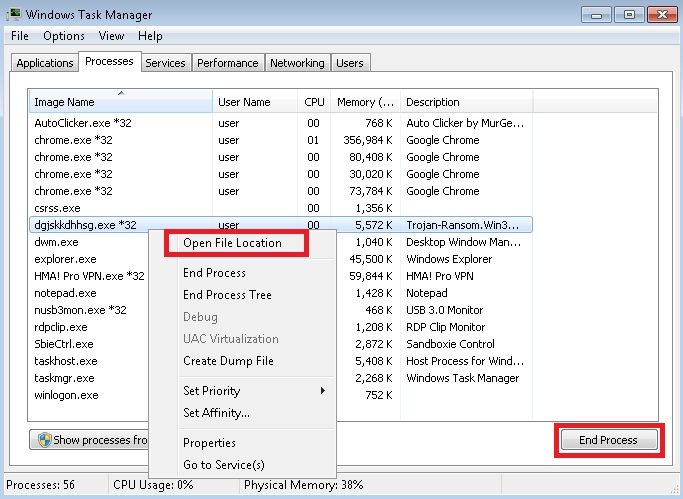
- Locate any suspicious processes associated with Amagnus@india.com encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Amagnus@india.com encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]
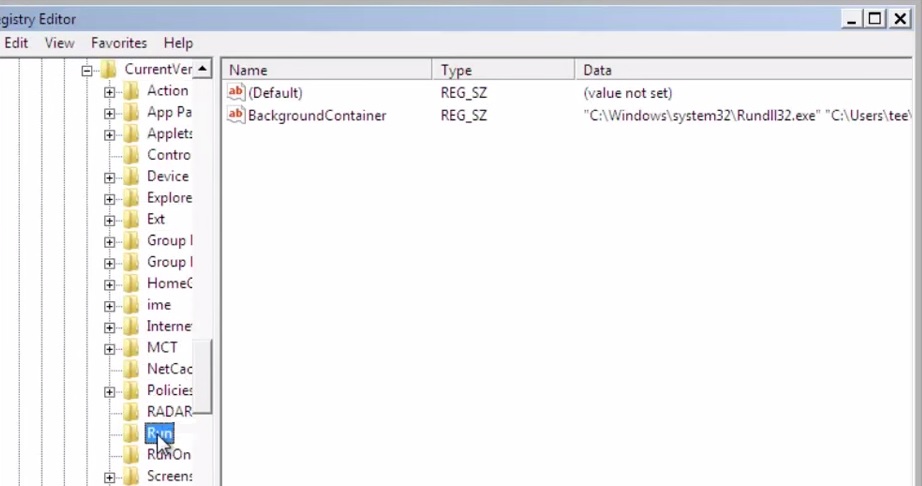
- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.
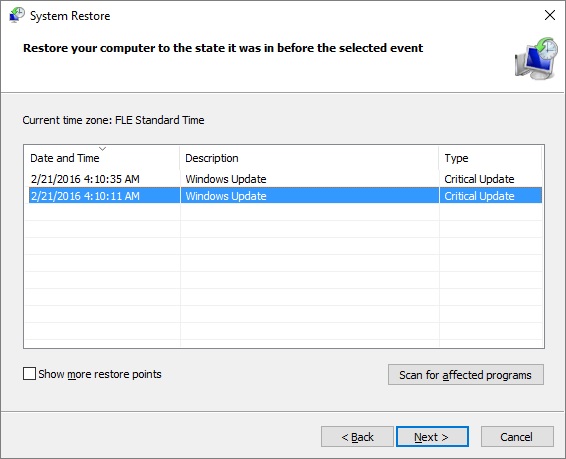
- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.



