Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Cerber 5.0.1 Ransomware?
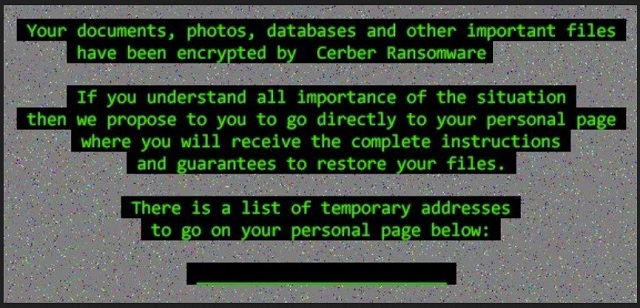
Readers recently started to report the following message being displayed when they boot their computer:
“Attention! Attention! Attention! Your documents, photos, databases and other important files have been encrypted!”
Just when you though the Cerber threat had died off, or at least quieted down, BAM! It strikes again! The original program got another ‘upgrade,’ and evolved again. It’s just as dangerous and damaging as all the previous variants, plaguing users. So, don’t take it lightly. It’s a threat you must NOT underestimate. As are all ransomware tools. Cerber 5.0.1 is the newest member to the Cerber family. It’s not particularly astonishing in its design as it follows the standard programming. The tool finds a sneaky way into your system. And, once it manages to slither in undetected, that’s it. It takes over. The infection spreads its clutches throughout every corner of your system. It gets a hold of every bit of information you have. All your pictures, documents, music, videos, everything. It’s no longer yours. It belongs to Cerber 5.0.1. The nasty tool locks it. It encrypts it, and demands a ransom for its release. If you wish to free your files, you have to pay a ransom. That’s how these tools work, hence the name ‘ransomware.’ But here’s the thing. These tools are a true plague. They play dirty. They are designed by wicked cyber criminals. You can’t win the fight against them. Every possible scenario ends badly for you. That’s because you’re set up for failure from the start. The game is rigged. So experts advise against any sort of participation. Don’t engage with the extortionists! Don’t contact them! Don’t pay them! Don’t follow their demands! Do nothing! Cut your losses. The best course of action you can take is to let go of your data. Yes, it’s harsh. But files are replaceable. Is your personal or financial information? If you pay, you expose it. So, keep your private life private! Forsake your files.
How did I get infected with?
Like its predecessors, and other ransomware, Cerber 5.0.1 preys on carelessness to sneak in. The tool used it against you as a means of invasion. It used your distraction, haste, and naivety to gain access to your system. All, while keeping you clueless. Confused? Let’s elaborate. The tool needs your ‘Okay’ to enter your PC. It has to ask whether you agree to let it into your system before it invades. In other words, you agree to its installment. And, you have no memory of doing so. But how does that happen? Well, the infection does have to ask. Bu it doesn’t have to do it openly. So, it uses every known trick in the book to do it sneakily. Cerber 5.0.1 can pretend to be a bogus system or program update. Like, Adobe Flash Player or Java. It can hitch a ride with freeware or spam email attachments. It can hide behind corrupted sites or links, as well. The tool has its pick of methods of infiltration. But each one relies on your carelessness. Neither one can succeed without it. Instead of throwing caution to the wind when installing updates or tool, be vigilant! Read the terms and conditions. Don’t just rush to say ‘Yes.’ Do your due diligence! Sometimes even a little extra attention can save you a ton of troubles.
Why is Cerber 5.0.1 dangerous?
After Cerber 5.0.1 slithers into your system, and settles, it gets to work. The tool uses the usual algorithm to encrypt everything you keep on your PC. It adds an extension at the end of each file, and locks it. Your videos, pictures, music, etc. Once the extension gets added, that’s it. You can no longer access anything. You can move them, try to rename them. It’s all for not. Anything other than applying the decryption key proves futile. That’s what the ransomware states in its ransom note, as well. After the encryption process finishes, the tool leaves you a note. You can find it on your Desktop, as well as every folder, containing encrypted data. More often than not, it’s a TXT file, and it states the same thing over and over again. It’s something along the lines of: “Your files are encrypted. Pay us if you want to decrypt them.” The ransom amount shifts, but hat remains the same is the currency. It tends to always be in Bitcoin. What you have to understand, though, is that payment does NOT equal decryption. Here’s why. Even if you comply to the fullest, you can still lose your data. That’s because you’re dealing with cyber criminals. They WILL double-cross you. You can pay the ransom, even though it’s ill-advised to do so. But then what? You have ZERO guarantees that you’ll even receive a decryption key. Let alone that it will be the one you need. And, even if the starts align, and you get the right one, what then? The key gets rid of the encryption, not the infection. So, the ransomware still remains on your PC. Cerber 5.0.1 can still cause trouble. Nothing prevents the nasty tool from encrypting your files once more. Only this time, you have less money. And, what’s much, much worse, an exposed private life. After all, by paying the ransom the first time, you provide private information. You provide your personal and financial details. And, these criminals, these extortionists, get their hands on it. Are you okay with that? Think about what’s more important to you: pictures or privacy.
Cerber 5.0.1 Removal Instructions
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Cerber 5.0.1 Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.
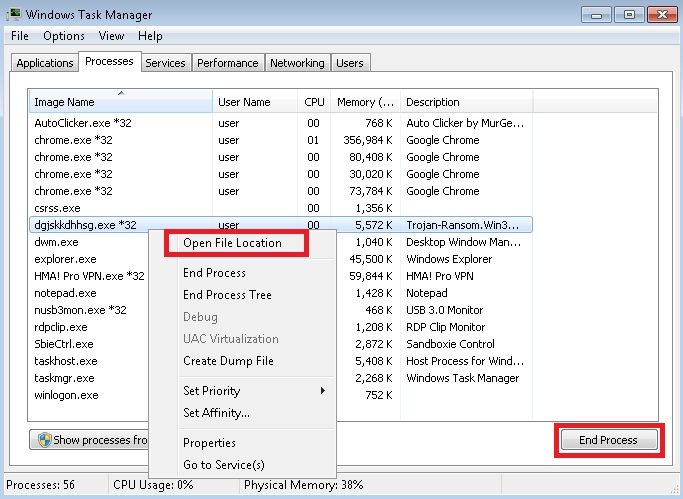
- Locate any suspicious processes associated with Cerber 5.0.1 encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Cerber 5.0.1 encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]
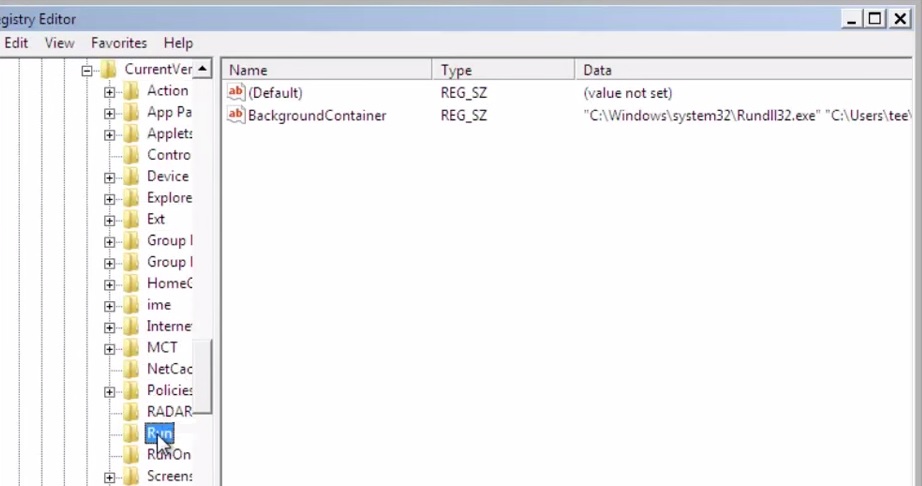
- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.
- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.