Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Digisom Ransomware?
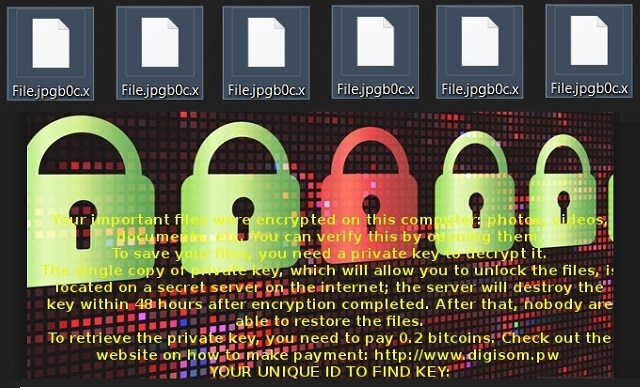
Readers recently started to report the following message being displayed when they boot their computer:
Your important files were encrypted on this computer: photos, videos, documents, etc. You can verify this by opening them.
To save your files, you need a private key to decrypt it.
The single copy of private key, which will allow you to unlock the files, is located on a secret server on the internet; the server will destroy the key within 48 hours after encryption completed. After that, nobody are able to restore the files.
To retrieve the private key, you need to pay 0.2 bitcoins. Check out the website on how to make payment: http://www.digisom.pw
YOUR UNIQUE ID TO FIND KEY:
Digisom Ransomware is a file-encrypting virus. In other words, it will lock your data and demand money from you. The parasite adds a [3_random_characters.x] extension to your files. What does that mean? It means Music.mp3, for example, gets renamed to Music.mp3.hU5.x. Needless to say, this brand new extension is a sign that your files are encrypted. Ransomware programs are among the biggest pests you could get stuck with online. Most PC users cringe at the very mentioning of file-encrypting infections. They have a reason to do so. The Internet is now filled with dangerous, aggressive ransomware parasites. The Digisom Virus doesn’t deviate from the classic pattern. As soon as it gets downloaded, this program scans your device. It locates your personal files that way. Eventually, encryption begins. Ransomware utilizes a strong cipher to modify all your private data. That includes a huge variety of formats and leads to a complete mess on your computer. For starters, all your precious data gets renamed. It now has a new format which your machine is unable to recognize. And no, you can’t use your files. Digisom Ransomware takes down pretty much all your personal information. Starting with your photos, the virus also locks music, videos, presentations, documents. You’re being denied access to all your files. It goes without saying that will inevitably cause you some trouble. The only way to avoid damage is by having backups of your important files. Don’t be gullible to think ransomware cannot get to you. It can and, unless you think in advance, it might cause you harm. Digisom Ransomware drops 10 files named Digisom Readme0.txt to Digisom Readme9 on your desktop. Those are your payment instructions. According to the ransom notes, you have to make a payment. The only problem is that paying guarantees you absolutely nothing. Hackers aren’t the right people to make negotiations with. As you could imagine, freeing your files is their very last concern. Crooks are much more focused on stealing your money so keep that in mind. You’re supposed to receive a decryptor in exchange for your Bitcoins. The sum demanded is 0.2 Bitcoins which equals almost 200 USD at the moment. Are you willing to give hackers 200 dollars and get scammed? No? Then ignore the parasite’s empty promises/threats. What you should do is tackle the parasite as soon as possible.
How did I get infected with?
It’s quite difficult to determine the infiltration method Digisom Ransomware used. However, there are a couple of popular techniques hackers tend to use. For instance, spam messages and emails. This is probably the oldest technique out there. As you can see, though, it is still popular and effective. All sorts of parasites apply it including Trojan horses, browser hijackers, etc. Next time you receive something suspicious, just delete it. Having to remove an infection afterwards is a much more troublesome activity. Beware of spam email-attachments and messages from unknown senders. Also, stay away from illegitimate websites and third-party pop-ups. There are fake software updates and corrupted program bundles as well. Ransomware often gets spread via exploit kits or with the help of Trojans. To sum up, there are many ways to end up infected with ransomware. Instead of being negligent, pay attention to your safety. No cyber intruder is to be underestimated. Last but not least, stay away from random, unverified torrents. Hackers are full of ideas when it comes to malware so you cannot afford any mistakes.
Why is Digisom dangerous?
Digisom Ransomware is a highly dangerous infection. Not only does it encrypt your private data but it also attempts to steal your money. This is nothing but a cyber scam. Instead of falling straight into hackers’ trap, get rid of the parasite. Make sure you ignore Digisom Ransomware’s ransom notes even though those are quite intimidating. The virus even gives you a deadline. You’re supposed to make the payment in 48 hours. If not, hackers will delete the decryption key. However, you might follow the instructions ASAP and still receive absolutely nothing in return. Crooks aren’t really known for being honorable people, are they? Restrain yourself from paying the money demanded unless you want to get scammed. Ransomware allows hackers to involve you in a nasty fraud so don’t let them. To delete the parasite manually, please follow our detailed removal guide down below.
Digisom Removal Instructions
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Digisom Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.
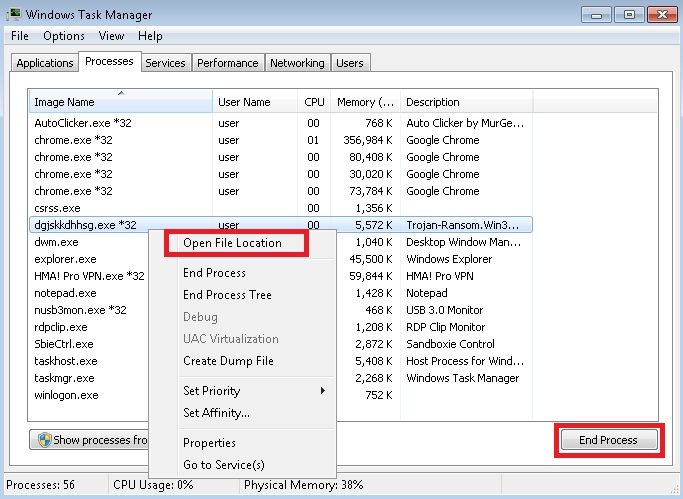
- Locate any suspicious processes associated with Digisom encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Digisom encryption Virus startup location
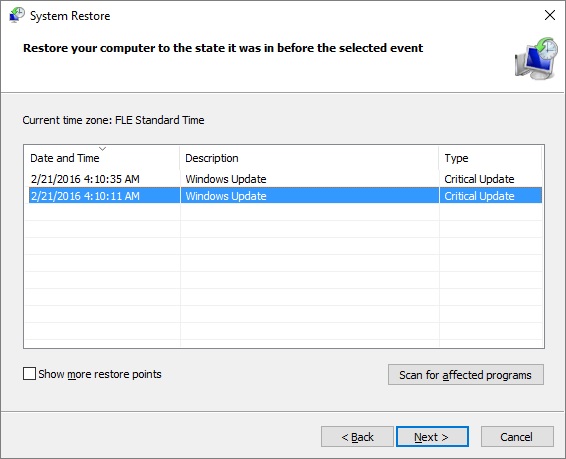
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]
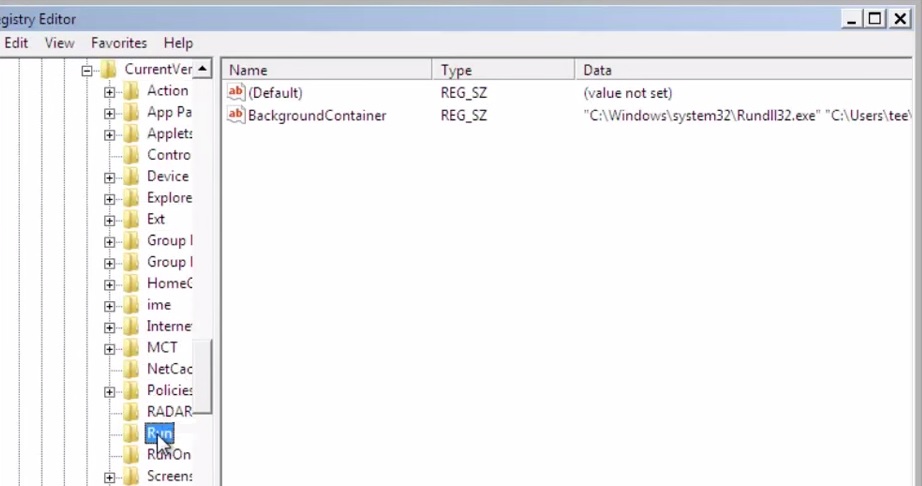
- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.
- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.