Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
This article can help you to remove Smokeloader Virus. The step by step removal works for every version of Microsoft Windows.
Smokeloader is yet another invasive Trojan horse. This virus is quite effective and has been on the black market since 2011. If it has infected your device, your predicaments are not great. Smokeloader Trojan is a backdoor to your system. It can download and install malware. In the past few years, the Trojan was used for malware and ransomware distribution. The hackers can use it to cause a mess on your computer. Once on board, Smokeloader corrupts your system’s key files and processes. The parasite can modify your system registry. It can cause some program of yours to crash and stop working. Like, your anti-virus software for example. The Trojan is dangerous. It can see your MAC and IP addresses, and your registration key. This information will be sent to the crooks. They can use it to target you with some scam or to blackmail you. The Trojan is exposing you to numerous threats. It roots deeply in your OS. It loads together with your system and runs on it. It has no visualization and is hard to be detected. It can do whatever it won’t and you won’t even realize what has happened before it is too late. In fact, you are quite lucky to know that it is on board. It can spend months without being detected. Smokeloader Trojan is quite a sophisticated parasite. It can even update itself. Don’t fool yourself. Its creators work hard on the virus. With every passing day, the Trojan becomes more and more dangerous. Don’t waste your luck. Now that you know about the Trojan, remove it as soon as possible. We have provided a manual removal guide. However, this Trojan is very complex. Its removal requires a bit more advanced skills. If you fail to remove all components of the infection, the Trojan will re-install itself. If you delete wrong files, on the other hand, you will end up with the Blue Screen of Death. Therefore, we recommend you to use a trustworthy anti-malware application. This is the safest and easiest way to deal with the infection.
How did I get infected with?
Smokeloader Trojan is distributed via exploit kits. Basically, to infect your device, the Trojan uses vulnerabilities in your software. That’s why it is important to update your programs regularly, especially your anti-virus app. Smokeloader Trojan is also spread via phishing emails, torrents, and fake software updates. Your caution, though, can prevent these techniques from succeeding. If you receive a message from a stranger, verify the sender before you open the letter. You can enter the questionable email address into some search engine. If you are lucky, you will find evidence online. The crooks tend to write on behalf of well-known organizations, companies, banks, post offices, police departments, etc. When you receive such a message, go to the company’s official website and compare the email addresses listed there with the one you have received a message from. If they don’t match, delete the pretender on the spot! Also, when you such an email, opt for red flags. A reliable company would use your real name to address you. If the letter starts with “Dear Customer” or “Dear Friend,” proceed with caution. Do not click on links and don’t download anything unless you are absolutely sure that the file is safe. Scan the downloads with a trustworthy anti-virus app.
Why is this dangerous?
Smokeloader Trojan is very hazardous. It cannot be beneficial to you. On the contrary. It is a giant hole in your security. The Trojan is known to install ransomware in the past. It can install any program. It can also uninstall your software. What is worse, it may cause the Blue Screen of death. Unfortunately, we cannot tell you what will happen to your machine. The hackers behind Smokeloader Trojan can use it as they see fit. This parasite gives them control over your machine. The Trojan can install malware which enables remote control of your PC, for example. Or, it can turn your device into a part of a botnet. Keep in mind that being part of an illegal bonnet is reason enough for a legal prosecution to take place. Don’t risk getting in trouble with the authorities. You should take immediate action against Smokeloader!
Manual Smokeloader Removal Instructions
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
The Smokeloader infection is specifically designed to make money to its creators one way or another. The specialists from various antivirus companies like Bitdefender, Kaspersky, Norton, Avast, ESET, etc. advise that there is no harmless virus.
If you perform exactly the steps below you should be able to remove the Smokeloader infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
STEP 1: Track down Smokeloader related processes in the computer memory
STEP 2: Locate Smokeloader startup location
STEP 3: Delete Smokeloader traces from Chrome, Firefox and Internet Explorer
STEP 4: Undo the damage done by the virus
STEP 1: Track down Smokeloader related processes in the computer memory
- Open your Task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Carefully review all processes and stop the suspicious ones.
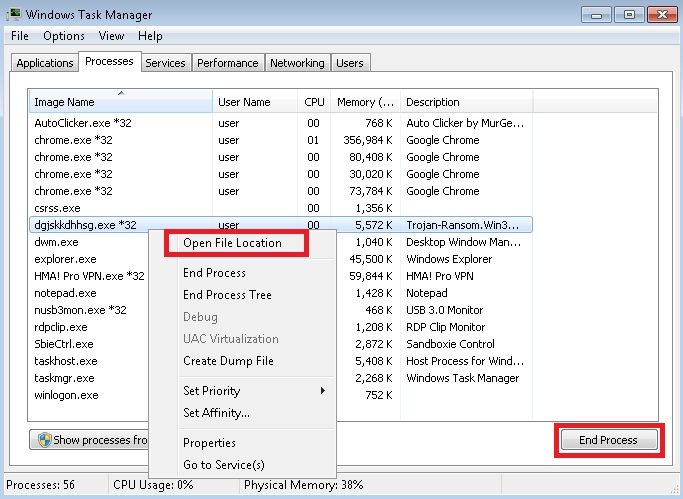
- Write down the file location for later reference.
Step 2: Locate Smokeloader startup location
Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
Clean Smokeloader virus from the windows registry
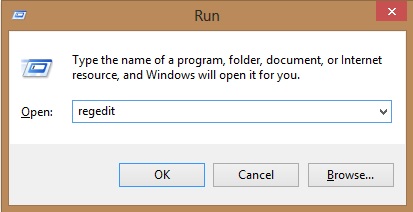
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]
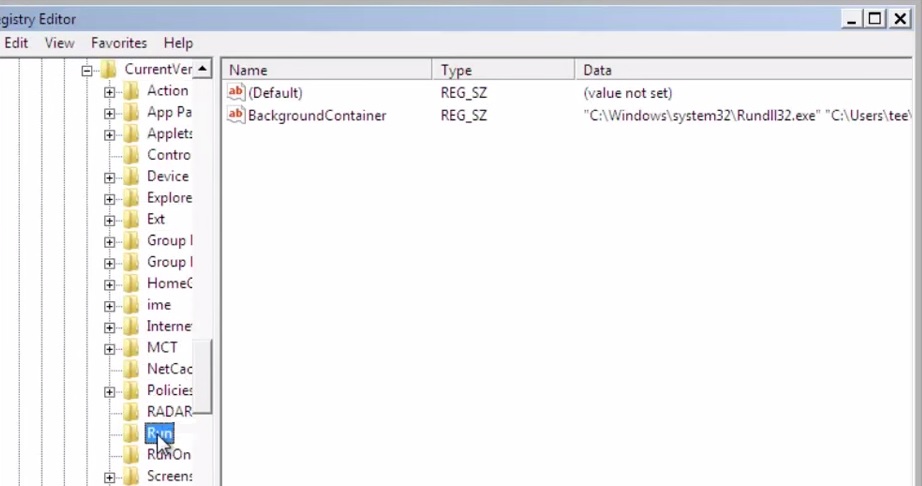
- Then open your explorer and navigate to: %appdata% folder and delete the malicious executable.
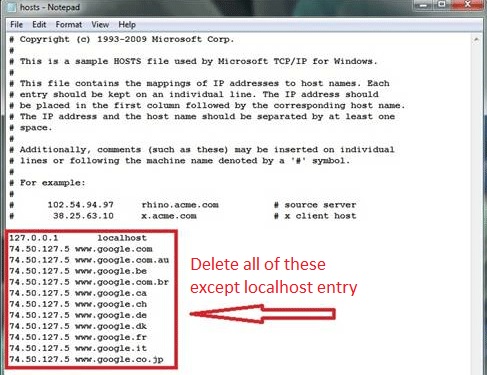
Clean your HOSTS file to avoid unwanted browser redirection
Navigate to %windir%/system32/Drivers/etc/host
If you are hacked, there will be foreign IPs addresses connected to you at the bottom. Take a look below:
Step 4: Undo the possible damage done by Smokeloader
This particular Virus may alter your DNS settings.
Attention! this can break your internet connection. Before you change your DNS settings to use Google Public DNS for Smokeloader, be sure to write down the current server addresses on a piece of paper.
To fix the damage done by the virus you need to do the following.
- Click the Windows Start button to open the Start Menu, type control panel in the search box and select Control Panel in the results displayed above.
- go to Network and Internet
- then Network and Sharing Center
- then Change Adapter Settings
- Right-click on your active internet connection and click properties. Under the Networking tab, find Internet Protocol Version 4 (TCP/IPv4). Left click on it and then click on properties. Both options should be automatic! By default it should be set to “Obtain an IP address automatically” and the second one to “Obtain DNS server address automatically!” If they are not just change them, however if you are part of a domain network you should contact your Domain Administrator to set these settings, otherwise the internet connection will break!!!
- Check your scheduled tasks to make sure the virus will not download itself again.
How to Permanently Remove Smokeloader Virus (automatic) Removal Guide
Please, have in mind that once you are infected with a single virus, it compromises your whole system or network and let all doors wide open for many other infections. To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify possible virus leftovers or temporary files.