Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Odin Ransomware?
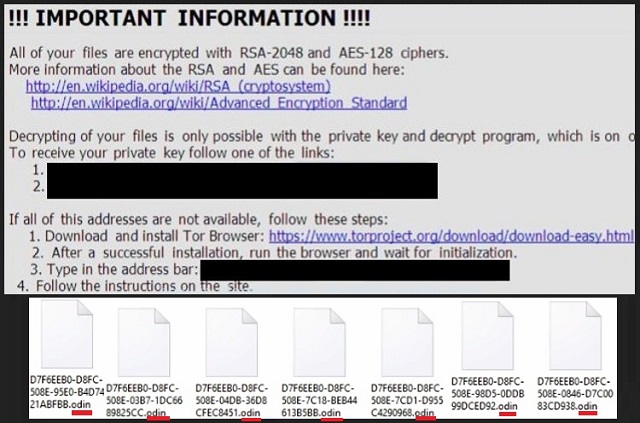
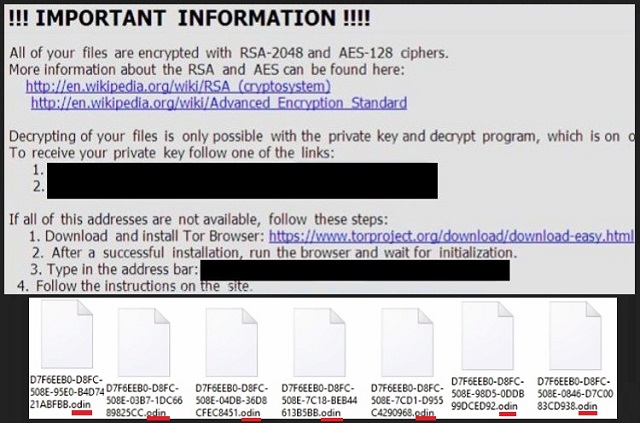
Reader recently start to report the following message being displayed when they boot their computer:
!!!! IMPORTANT INFORMATION !!!!
All of your files are encrypted with RSA-2048 and AES-128 ciphers.
More information about the RSA and AES can be found here:
hxxps://en.wikipedia.org/wiki/RSA_(cryptosystem)
hxxps://en.wikipedia.org/wiki/Advanced_Encryption_Standard
Decrypting of your files is only possible with the private key and decrypt program, which is on our secret server.
To receive your private key follow one of the links:
[edited]
If all of this addresses are not available, follow these steps:
1. Download and install Tor Browser: hxxps://www.torproject.org/download/download-easy.html
2. After a successful installation, run the browser and wait for initialization.
3. Type in the address bar: [edited]
4. Follow the instructions on the site.
!!! Your personal identification ID: [edited]
Funnily enough, hackers often draw inspiration from Norse mythology. Crooks seem to be quite fascinated with the mighty Gods from the North. Unfortunately, the results are devastating. One of the most problematic infections we’ve come across recently is the Locky Ransomware. We’ve already provided detailed removal instruction about this pest. The problem is, Locky was updated. It was revived and is now roaming the Web stronger than ever. You see where this is going, don’t you? The brand new version of the destructive Locky Ransomware landed on your computer. How does this infection work? It uses a combination of RSA-2048 and AES-CBC 256 encrypting ciphers to lock your files. You see, the virus mixes a symmetric with an asymmetric algorithm. As a result, anything this program encrypts, remains encrypted. Pictures and music and Microsoft Office documents and videos – all of this gets locked. The parasite takes down a huge variety of file formats. It denies you access to practically all data of value you’ve stored on the PC. Obviously, such tricks could cause you serious damage. In addition, you can’t view your favorite pictures and listen to your favorite music. Ransomware hasn’t just gotten the title “worst infection online”. Ransomware has earned it. This virus renames the target files and changes their formats. You’ll notice a bizarre. Odin extension that was added by the parasite. Now, this is how you know your files are inaccessible. Your computer can’t recognize the new file format. Logically, you won’t be able to use it. Ransomware turns your personal data into unreadable gibberish. It makes your files unusable. If you thought having your data encrypted was bad enough, wait till you hear the rest of it. While locking your information, the virus creates payment instructions. Why would you need them, you might ask? Because paying a certain sum of money is the only way to get your data back. Or so hackers claims. The ransomware creates _HOWDO_text.html and _HOWDO_text.bmp files. You will find those in all folders that contain encrypted data. It goes without saying that’s a lot of folders. The parasite also changes your desktop wallpaper as well. Its goal is to force the nasty ransom message on you all the time. Do yourself a favor and don’t pay anything.
How did I get infected with?
You might have opened some corrupted email. You might have installed malicious software. You might have also clicked on a fake product deal or some sort of third-party pop-up. As you can clearly see, ransomware travels the Web in various ways. It’s almost impossible to know exactly how this pest managed to get installed. However, there are some particularly popular infiltration techniques. Hackers’ favorites, if you will. Ransomware usually gets send straight to your inbox. Hence, stay away from random email-attachments and spam emails. Same thing goes for messages from unknown senders. One single click could set free some vicious piece of malware. Are you willing to risk it? If not, watch out what you click open. Infections may pretend to be emails from shipping companies or even job applications. Delete what you don’t trust and be cautious online. Also, avoid illegitimate websites, torrents, freeware bundles. More often that not, those are harmful. Last but not least, the virus might have sneaked in with the help of a Trojan. Check out your PC for more parasites; you won’t regret it.
Why is Odin dangerous?
Once the virus lands on board, it scans your machine. This way, it locates all your private information. Then the encryption process begins. As mentioned already, a rich variety of file formats falls victim to the ransomware. Crooks lock your data and hold it hostage. Furthermore, they directly ask for money. Hackers offer you a deal. You’re supposed to pay a ransom in Bitcoin (online currency) to receive a decryptor. It goes without saying that paying the money would be a terrible idea. Just think about it; you’d be making a deal with greedy cyber criminals. The only thing they’re interested in is stealing your money. This is why ransomware is on the rise right now – it helps crooks gain easy profit. The thing is, hackers’ illegitimate revenue comes at your expense. Remember, these programs are attempts for some nasty cyber frauds. Keep your Bitcoins and don’t let hackers blackmail you. Get rid of the ransomware as soon as possible. To do so manually, please follow our detailed removal guide down below.
Odin Removal Instructions
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Odin Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- This particular Ransomware use a legitimate windows executable called rundll32.exe to inject its malicious payload locate in %Temp%\[name_of_dll],qwerty
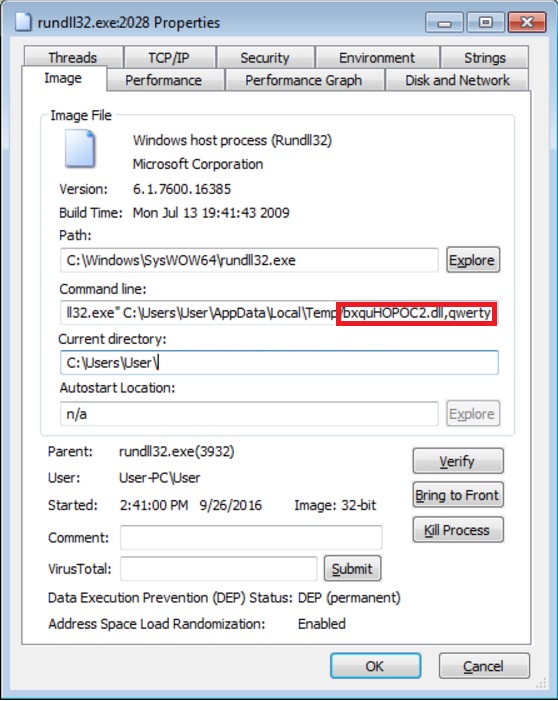
- Before you kill the process, type the name on a text document for later reference.
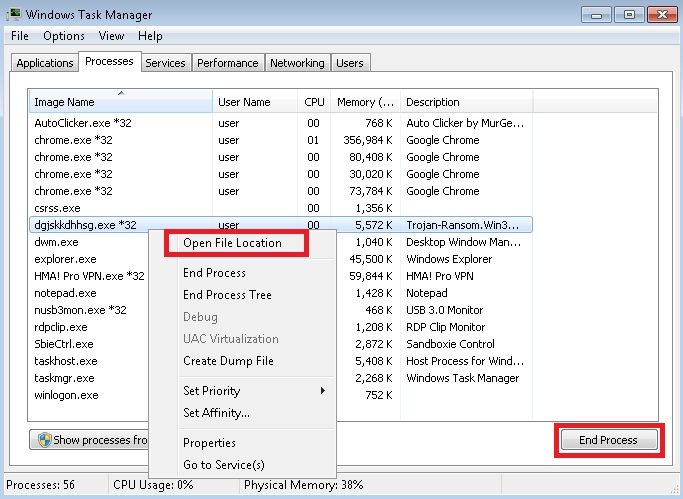
- Locate any suspicious processes associated with Odin encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
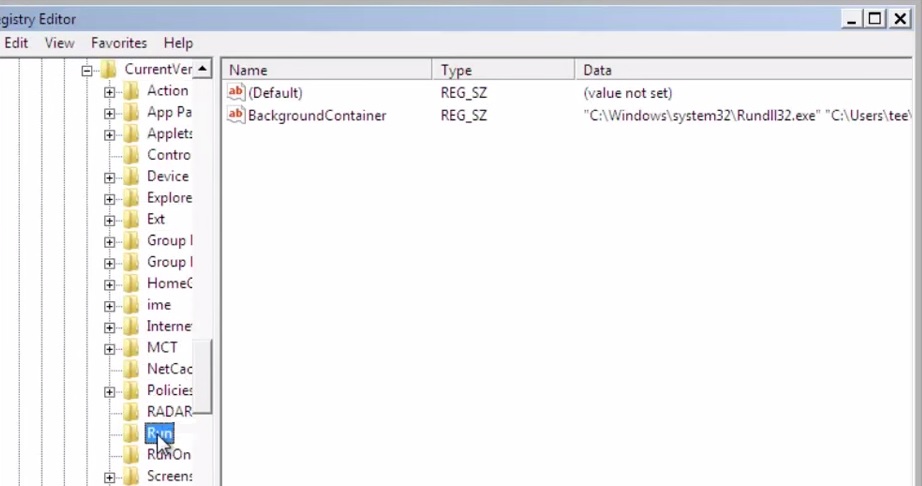
STEP 3: Locate Odin encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]
- Then open your explorer and navigate to:
Once executed, the Odin ransomware will encrypt victim’s files, rename them, and then append the .ODIN extension. For example, test123.jpg may be renamed as 4G3O55IG-F457-7FED-2X7B-5B22862C4421.odin.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
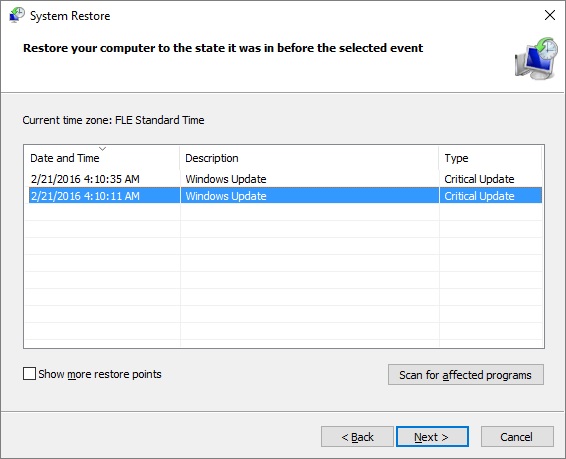
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.
- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.