Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Can’t Remove Remove 19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF Malware pop-ups?
19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF is a Bitcoin address. It’s an address, you get asked to use, and send money to. Don’t do that. Cyber criminals feed you lies, and extort you for monetary gain. You’re the victim of a scamware. Despite what these extortionists will have you believe, there’s no Trojan on your PC. There’s a scamware infection. The people, behind it, try to threaten you into acting against your best interest. They feed you lies, and hope you fall for them. They feed off of your naivety and fear. Don’t believe their tricks. You’ve fallen prey to quite the standard scam. Let’s explain. A scamware slithers into your PC, undetected. You then receive a rather scary email. It’s full of frightening statements and threats. It claims that the cyber criminals have access to compromising data. Data, you’d rather keep private. The email, then, ends with a demand for a ransom payment. You get asked to send said payment to the 19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF address. Supposedly, once you do, all your secrets remain secret. If not, the cyber criminals threaten to expose the data to your contacts, friends, and family. Don’t fall prey to the scheme. Try to stay level-headed, and look past the deception. There’s no Trojan on your computer. These people don’t have access to your private data. Don’t pay them a dime! Don’t contact them at all. Don’t waste your time, energy and money, dealing with them. Acknowledge the presence of the scamware. And, act against it the first chance you get. The sooner you remove it from your computer, the better.

How did I get infected with?
How do you suppose you got stuck with scamware? These types of tools don’t appear out of thin air. Their presence may take you by surprise, but it’s your fault they’re lurking on your PC. Let’s explain. These infections prey on your carelessness to invade. They use all manner of tricks to slip past you undetected. They can only invade, if you’re careless enough not to spot them. If you’re vigilant, however, you can catch the tool in the act. You can spot it, attempting infiltration, and keep it out of your PC. Caution helps you to keep an infection-free PC. The lack thereof has the opposite outcome. Cyber threats, like the scamware, prey on your carelessness. They rely on your distraction, haste, and naivety to ensure their covert infiltration. They need you to rush, and skip doing due diligence. To leave your fate to chance, and not bother with vigilance. Don’t oblige. Don’t ease the infection’s invasion. Make sure to take the time to be thorough. Remember that even a little extra attention can save you countless troubles.
Why are these ads dangerous?
The email you receive is full of falsehoods. It tries to convince you that your system got hacked. And, the hacker gained access to your camera. And, then, utilized it to stockpile compromising pictures of you. And, it continues with a threat. Unless you want these pictures to get exposed to the public, you must comply. You have to follow the hackers’ demands. Meaning, you must pay a ransom. The exact amount tends to vary. But it’s usually between 500 and 800 US Dollars. You’re expected to pay in Bitcoin. And, send the sum to the 19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF address. You’re even given a deadline – two or three days to complete the demands. These people try to blackmail you, and profit off of your gullibility. Don’t let them monetize your fear. Don’t fall for their deception. Pay them nothing! Instead of following the requests of cyber criminals, find where the scamware lurks. Try to locate its exact hiding place on your computer. And, once you do, get rid of it. It’s the best course of action, you can take. Take it ASAP.
How Can I Remove Remove 19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF Malware Pop-ups?
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
If you perform exactly the steps below you should be able to remove the infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
STEP 1: Uninstall suspicious software from your Add\Remove Programs
STEP 2: Delete unknown add-ons from Chrome, Firefox or IE
STEP 1 : Uninstall unknown programs from Your Computer
Simultaneously press the Windows Logo Button and then “R” to open the Run Command
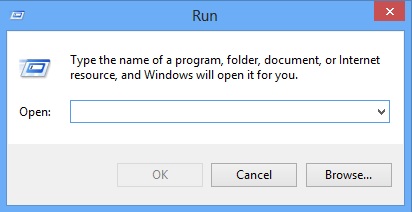
Type “Appwiz.cpl”
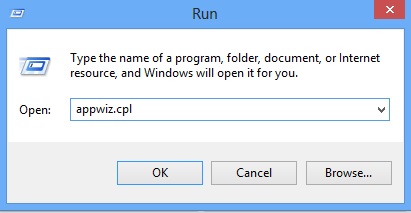
Locate the any unknown program and click on uninstall/change. To facilitate the search you can sort the programs by date. review the most recent installed programs first. In general you should remove all unknown programs.
STEP 2 : Remove add-ons and extensions from Chrome, Firefox or IE
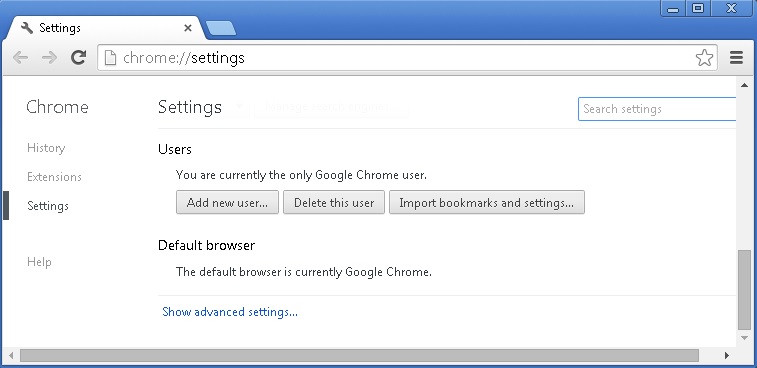
Remove from Google Chrome
- In the Main Menu, select Tools—> Extensions
- Remove any unknown extension by clicking on the little recycle bin
- If you are not able to delete the extension then navigate to C:\Users\”computer name“\AppData\Local\Google\Chrome\User Data\Default\Extensions\and review the folders one by one.
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
- If you are using the latest chrome version you need to do the following
- go to settings – Add person
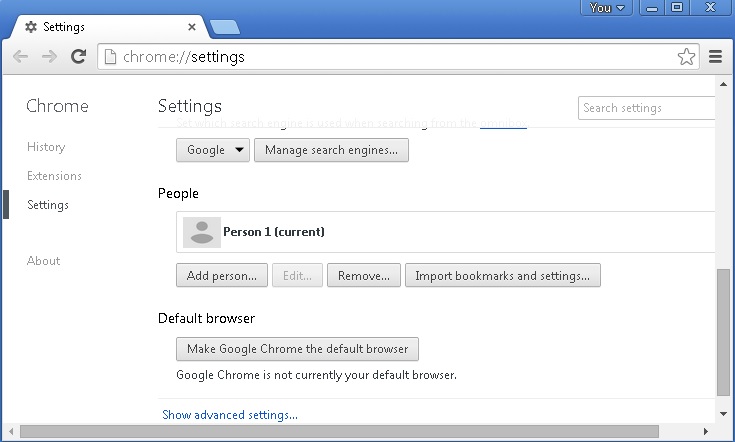
- choose a preferred name.
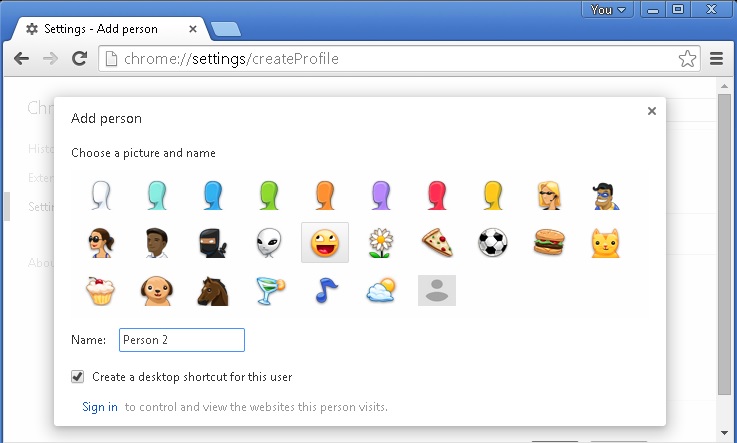
- then go back and remove person 1
- Chrome should be malware free now
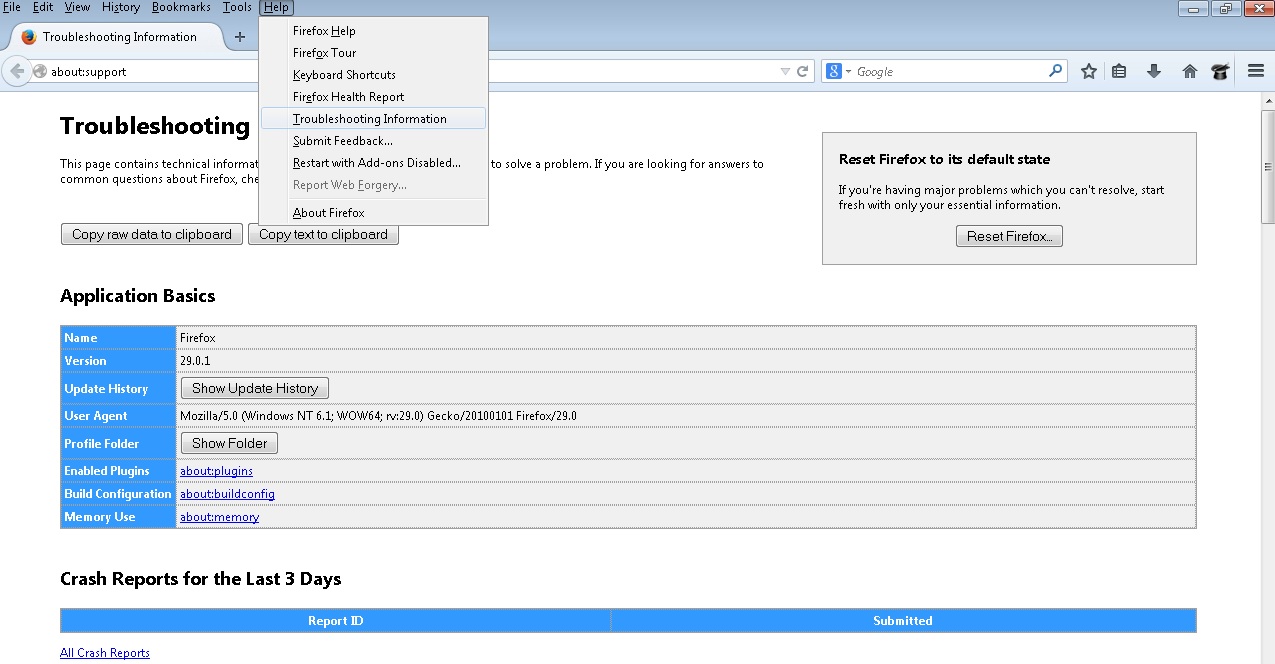
Remove from Mozilla Firefox
- Open Firefox
- Press simultaneously Ctrl+Shift+A
- Disable and remove any unknown add on
- Open the Firefox’s Help Menu
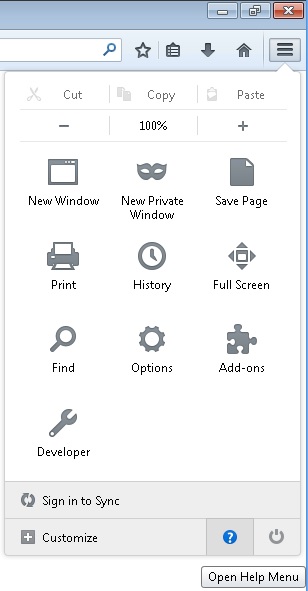
- Then Troubleshoot information
- Click on Reset Firefox
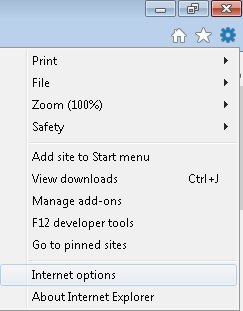
Remove from Internet Explorer
- Open IE
- On the Upper Right Corner Click on the Gear Icon
- Go to Toolbars and Extensions
- Disable any suspicious extension.
- If the disable button is gray, you need to go to your Windows Registry and delete the corresponding CLSID
- On the Upper Right Corner of Internet Explorer Click on the Gear Icon.
- Click on Internet options
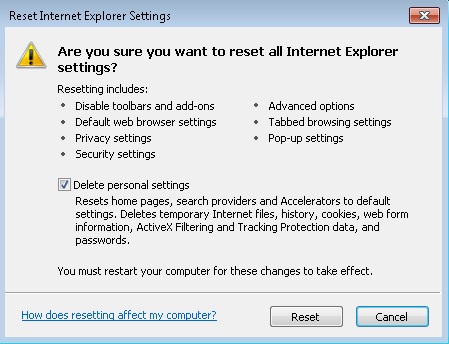
- Select the Advanced tab and click on Reset.
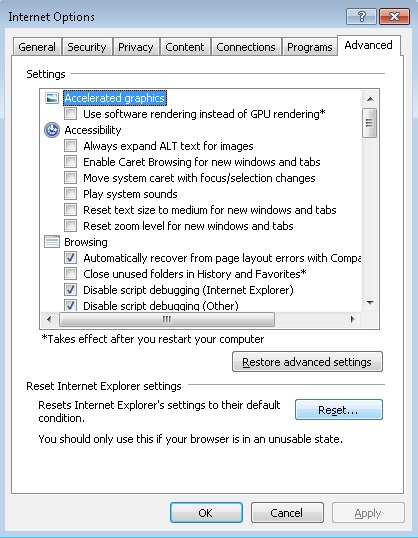
- Check the “Delete Personal Settings Tab” and then Reset
- Close IE
Permanently Remove Remove 19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF Malware Leftovers
To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify any registry leftovers or temporary files.