Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Anatova Ransomware?
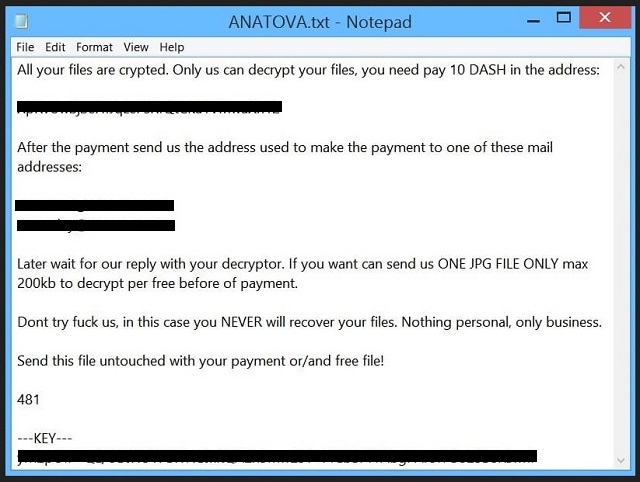
Readers recently started to report the following message being displayed when they boot their computer:
All your files are crypted. Only us can decrypt your files, you need pay 10 DASH in the address:
XpRvUwSjSeHfJqLePsRfQtCKa1VMwaXh12
After the payment send us the address used to make the payment to one of these mail addresses:
anatova2@tutanota.com
anatoday@tutanota.com
Later wait for our reply with your decryptor. If you want can send us ONE JPG FILE ONLY max 200kb to decrypt per free before of payment.
Dont try fuck us, in this case you NEVER will recover your files. Nothing personal, only business.
Send this file untouched with your payment or/and free file!
481
—KEY—
–
—KEY—
The Anatova cyber threat belongs to the ransomware family. It breaks the mold, compared to other such threat. It doesn’t add extension at the end of your files to rename them. And, it doesn’t change their icons. Upon the completion of its encryption, files get rendered unusable. No extensions needed. The name of the menace derives from the ransom note, you get. It’s a text file that’s called ‘Anatova.txt.’ It contains pretty standard information. If you wish to unlock your locked data, you have to pay up. The ransom costs you 10 DASH cryptocoins. Upon payment, you’re expected to contact the cyber criminals via email. Then, once they get your money and email, you “wait for our reply with your decryptor.” And, that’s it. That’s all the instructions, you get. You’re supposed to accept your predicament. Comply and pay up. And, then, wait and hope for the best. Don’t do that. Don’t play the infection’s game and follow its instructions. Don’t reach out to these cyber extortionists. And, do NOT pay them a single dime. All that gets you is regret. Payment doesn’t ensure you getting your data back. What it does ensure is the loss of money. Save your cash, and put your faith into backups. And, not in strangers, with malicious intentions.
How did I get infected with?
Ransomware tools turn to deception and finesse to sneak in. Like, most online threats, they prey on carelessness. Yours. The Anatova threat relies on your distraction, haste and gullibility. They ease its covert invasion. And, help it to slip by you, undetected. Let’s explain. Most programs like it, use the usual antics to infiltrate your PC. They hide behind corrupted links, sites, or torrents. Pretend to be fake system or program updates, like Java or Adobe Flash Player. Or, turn to freeware and spam emails. These are among the easiest ways for the infection’s infiltration. That’s because, users are most careless, when dealing with them. When installing freeware, most users throw caution to the wind, and rely on luck. They skip reading terms and conditions, and agree to everything in blind faith. They leave their fate to chance. Instead of doing their due diligence. It’s pretty much the same with spam emails. Unless you’re careless, you might get duped. Say, you receive a seemingly legitimate email. It appears to come from a well-known company, like Amazon. You open it, and it has a link that you get asked to click on. Or, an attachment that gets presented as a receipt you need to download, and check to verify. Infections are rather crafty. It’s up to you to look past their trickery. And, not let them sneak past you, unnoticed. Always take the time to be thorough. Read terms and conditions, look for the fine print, and double-check everything. Don’t allow yourself to get surprised. Vigilance helps to keep an infection-free PC. The lack thereof leads to the opposite outcome. Make the right choice.
Why is Anatova dangerous?
The Anatova menace uses encryption algorithms to lock your data. It encrypts everything you keep on your PC. Pictures, videos, archives, music, documents. Nothing escapes its reach. Upon completing its encryption, Anatova leaves you the note. It provides you with its expectation, and leaves you to make your choice. To follow their demands, or not. Heed experts’ advice, and don’t. Think about your choices. If you pay, you’re left at the mercy of strangers. What if these people scam you? What if they get your money, and you get nothing? Yes, they promise to send you the decryption key, you need. But what guarantees do you have? None! You have zero guarantees that payment will change anything. The infection can choose not to send you a key. Or, send you one that doesn’t remove the encryption at all. And, even if it does, and you release your files from Anatova’s grip, what then? How long do you think that’ll be the case? Think about it. You have a ransomware on your computer. It encrypts your data. You pay money to decrypt it. If you do so, you still have a ransomware on your PC. The payment gets you a decryption key. And, the key removes the encryption, not the infection. The Anatova menace remains on board, ready to strike once more. And, if it does, you’re back at square one. That’s hardly a desirable outcome. Don’t waste your time, energy or money. Don’t pay the cyber extortionists, behind Anatova. Losing money won’t prevent you from losing your data.
Anatova Removal Instructions
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Anatova Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.
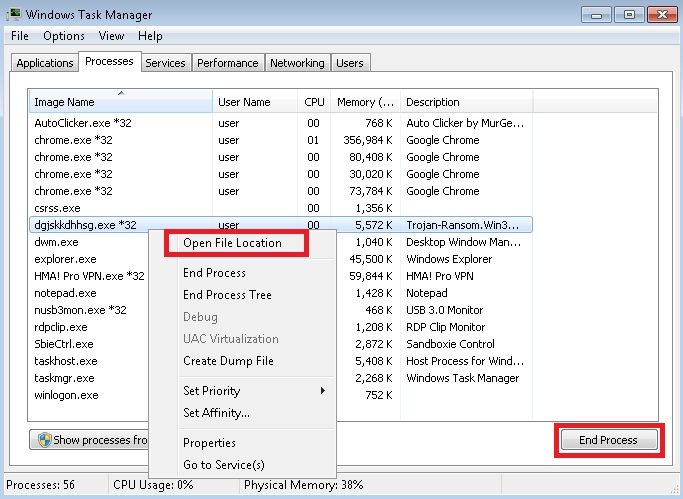
- Locate any suspicious processes associated with Anatova encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Anatova encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]
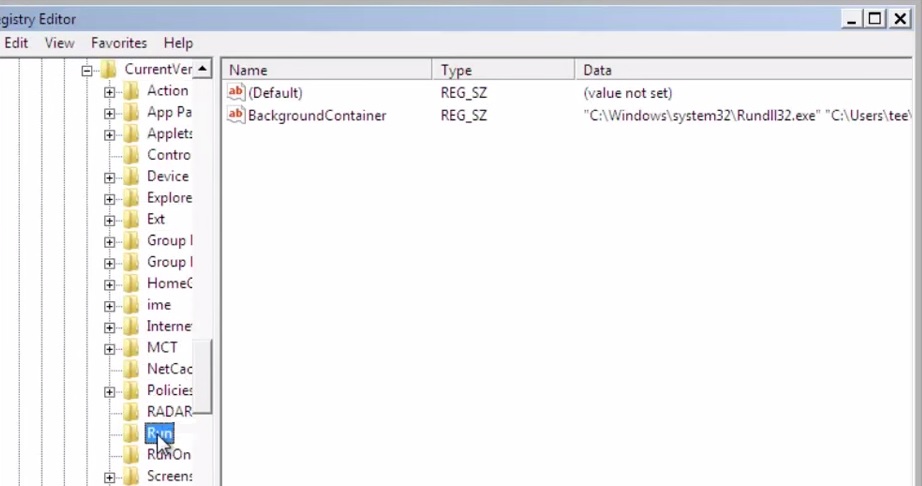
- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.
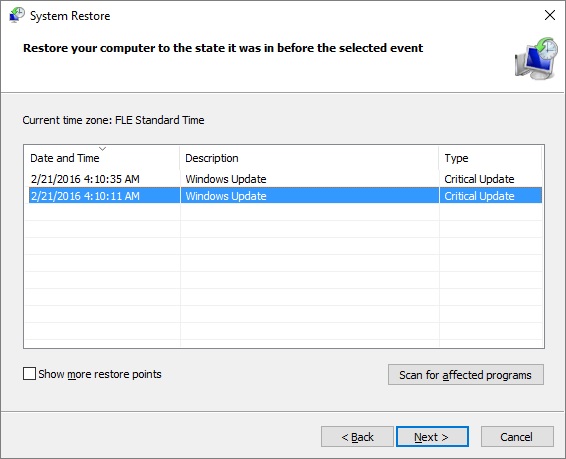
- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.


