Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Hese Ransomware?
Readers recently started to report the following message being displayed when they boot their computer:
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
—
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
To get this software you need write on our e-mail:
email
Reserve e-mail address to contact us:
email
Our Telegram account:
—
Your personal ID:
—
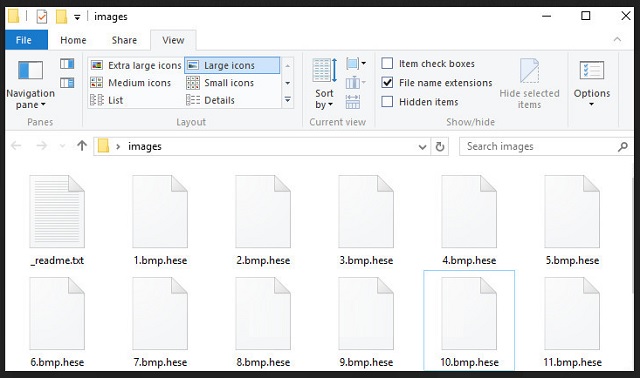
Hese is a nasty ransomware virus. It is based on the infamous STOP/DJVU Ransomware and is a complete and utter menace. It sneaks into your computer and detects the user-generated files. Pictures, music, databases, archives, documents – the ransomware identifies your files and encrypts them with strong encrypting algorithms. It marks the locked files by adding the .hese extension. Once it does so, you no longer have access to this file. You can still see the icons of your pictures, music, databases, but you can’t view nor edit these files. To get back your data, you need to open your wallet. Hese drops a ransom note (a file named _readnme.txt) at your desktop which includes a brief explanation of your situation, as well as lists the hackers’ demands. These criminals are shameless. They want $490 paid in Bitcoin. They also threaten to double the amount if you don’t contact them within 72 hours. The criminals, of course, provide email addresses which you can contact for additional instructions on how to pay the ransom. Do not make that mistake! You are dealing with experienced criminals. These people constantly improve their ransomware, as well as their blackmailing techniques. Contacting these manipulators won’t be beneficial to you. So, don’t waste your time and money. Consider discarding your files.
How did I get infected with?
Hese relies on classic distribution strategies. It uses spam emails and corrupted files to infect your device. The scheme is quite simple. The crooks flood your inbox with harmless-looking messages. They lure you into downloading their malicious files by describing them as offers, documents, or invoices coming from reputable organizations or websites. The files are usually well-known formats like .txt, .docx, or .pdf. If you download and scan the files, your anti-virus app is likely to mark them as safe, because the files themselves are not malicious. They don’t replicate themselves nor create other files. Once you open them, though, a message pops up that urges you to enable the file editing mode of your file-viewer. Do not make that mistake! A malicious script executes as soon as you click on that “Accept” button. The script downloads Hese which wastes no time and places its malicious files in system directories, as well as stats its encrypting operations.
Why is Hese dangerous?
Hese Ransomware holds your files as hostages and demands an astonishing ransom. Don’t open your wallet! You are dealing with experienced criminals. The people behind this virus have been in the ransomware business for a while. They know what they are during. Security researchers report that the newest versions of their ransomware can’t be decrypted by third parties. Paying the ransom, however, is not advisable as the crooks tend to ignore their victims once they receive the money. Quite often, the criminals don’t even have decryption tools for their viruses. Yes, Hese ransomware promises 1 free decryption as a proof of its operators’ abilities, yet, what guarantees do you have that the hacker won’t send you a nonfunctional tool? You can’t ask for a refund if this happens to you. The criminals demand Bitcoin. This currency is untraceable. No one can help you get your money back once you complete the transaction. Don’t become a sponsor of cyber-criminals! If you have file backups, you can use them to restore your data. Just make sure that Hese is completely removed before you attempt any such operations!
Hese Removal Instructions
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Hese Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.
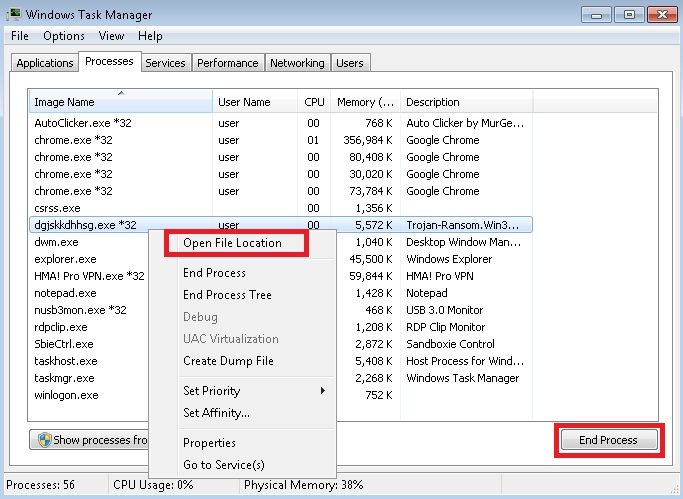
- Locate any suspicious processes associated with Hese encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Hese encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]
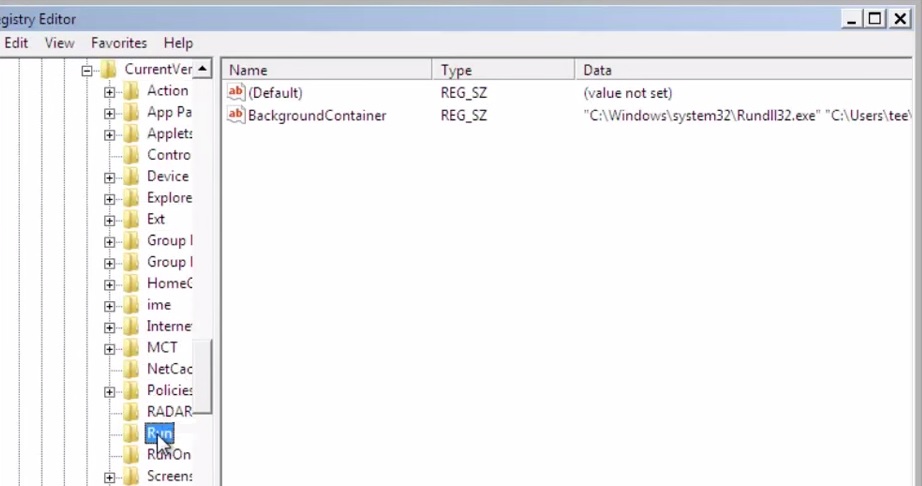
- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
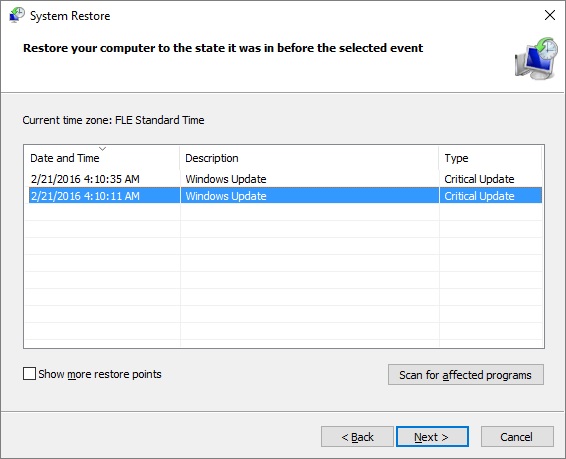
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.
- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.


