Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove UIWIX Ransomware?
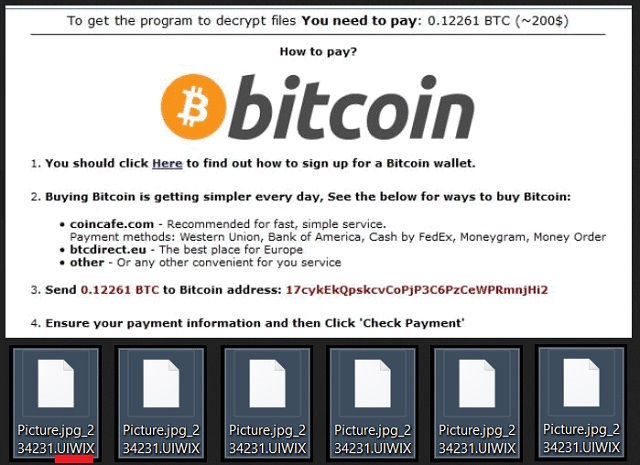
Readers recently started to report the following message being displayed when they boot their computer:
>>> ALL YOUR PERSONAL FILES ARE DECODED <<< Your personal code: {uniqueID} To decrypt your files, you need to buy special software. Do not attempt to decode or modify files, it may be broken. To restore data, follow the instructions! You can learn more at this site: {TOR-based web page} If a resource is unavailable for a long time to install and use the tor browser. After you start the Tor browser you need to open this link {TOR URL}
Have you heard of those viruses that lock your files and demand money to restore them? Well, UIWIX is the name of the newest member of their family. UIWIX is a classic ransomware. It uses trickery to slither into its victims’ computers. Of course, it won’t betray its cover until it is too late. UIWIX works in the background. The ransomware won’t waste time. It will start working at the moment it is installed. Its first step will be to scan your HDD and detect all target files. UIWIX can encrypt over ninety types of files, including documents, pictures, and archives. It adds the “.UIWIX” suffix at the end of all encrypted files. Thus, if you have a file named example.exe, the virus will rename it to example.exe.UIWIX. You will be able to see the icons of your files, yet, you can’t open or use them. Luckily, UIWIX doesn’t encrypt files that are essential for your OS. At least, you can use your computer to look for a solution. The bad news is, there is no free decryption tool, yet. However, security researchers are working on it. Therefore, don’t rush. Don’t contact the cooks. And most importantly, don’t pay the ransom. The hackers behind UIWIX demand 0.12 Bitcoins (about 220USD). In exchange, they will send you a description tool. Hackers have chosen this currency because it is impossible to be tracked down. Even the authorities won’t be able to help you if you don’t receive the decryption app. Don’t pay the ransom! You are dealing with criminals. You can’t expect them to play fair. They will double-cross you.
How did I get infected with?
There are many possible ways for UIWIX to reach your PC. Of course, spam emails are the most commonly used distribution technique. How many times have you heard not to open emails from strangers? Stop doing it already. Scammers are clever and imaginative. They will embed malicious code into all sorts of files. Before you download an attached file, check the sender’s contacts. Do so by entering the questionable email address into some search engine. If it was used for shady business, there might be evidence online. Don’t stop here. As we’ve already said, crooks are creative. New email accounts are created for different scams. If you are part of the first wave of spam emails, there won’t be any evidence online. So, double-check everything. If you receive a letter from your bank or any other organization, go to their official website. There, under the contact section, you can find their authorized email addresses. Compare them with the one you have received a message from. If they don’t match, delete the spam email immediately. Don’t risk your computer’s health. Do your due diligence. Stay away from shady websites and don’t follow links blindly. Neither should you neglect your anti-virus software. It is not hard to keep it up to date.
Why is UIWIX dangerous?
UIWIX has locked your personal files. There is no going back. The only way to restore them is to pay the demanded ransom. This is what the hackers want you to believe. However, there is always hope. Do you keep system backups on external devices? If you do, you can use them to restore your files for free. But, not before you remove the ransomware. Your first task should be the detection and removal of UIWIX. If you don’t do so, your newly restored files will be encrypted too. The virus will also corrupt your external memory. Therefore, use a trustworthy anti-virus program and remove the ransomware. Or, do it manually. Just follow our guide. UIWIX can and will modify your system registry. It will delete your shadow copies. So, don’t count on them. Backups on an external device are your only option. We recommend against paying the ransom. There are cases where the victims paid, yet, they did not receive a working tool. You are dealing with criminals. Never forget that. Consider discarding your data. Clean your machine and start backing up your system regularly. This way you will be prepared if ransomware strikes again.
UIWIX Removal Instructions
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover UIWIX Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.
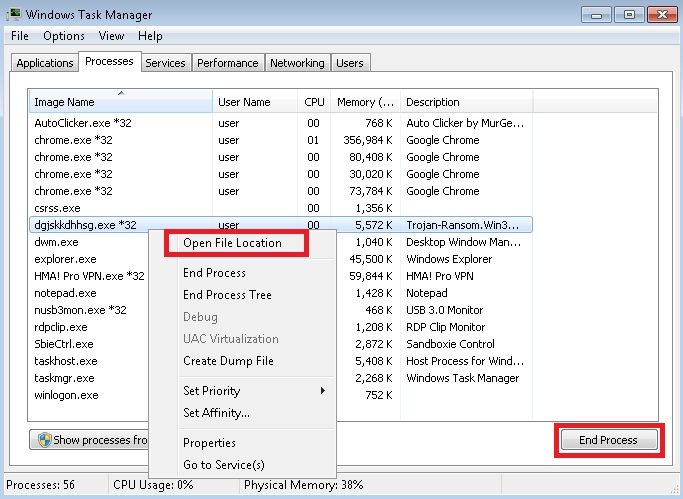
- Locate any suspicious processes associated with UIWIX encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate UIWIX encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]
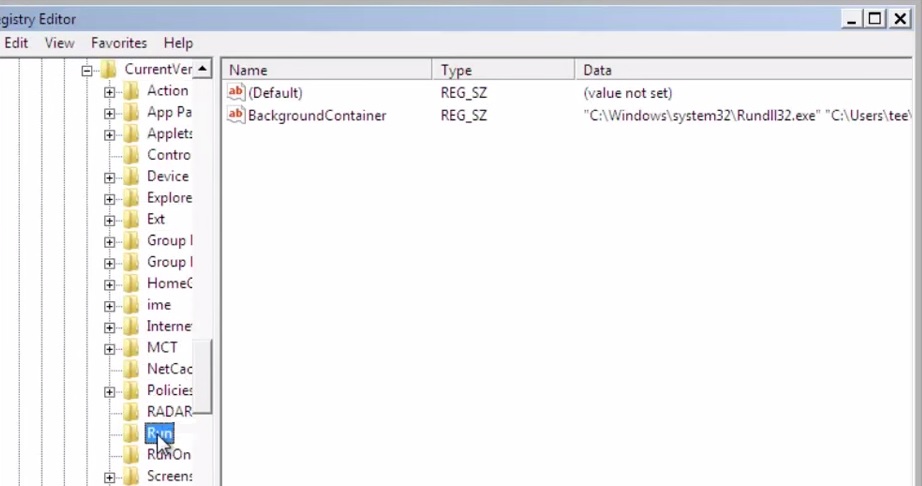
- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.
- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.