Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Yatron Ransomware?
Readers recently started to report the following message being displayed when they boot their computer:
your important files are encrypted !
Your documents, photos, databases and Other personal files are encrypted ?
the files that you looked for not readable ?
We are the only ones who can decrypt your files Through the unique key.
what should I do for decrypting my files?
If you want to recover your files, you must purchase a the unique key
send300$ btc to address:36Bz7B1gsc1WdBf7tnRNbKUGiQjQ2qHGoo
Send us your ID after your payment
Email to contact us : yatronraas@mail.ru
As proof you can email us 2 files to decrypt and we will send you the recover files
Amount Bitcoins: 300$
Your ID: –
Wallet for sending Bitcoins: 36Bz7B1gsc1WdBf7tnRNbKUGiQjQ2qHGoo
Contract Us: yatronraas@mail.ru
Yatron is a dangerous ransomware infection. It’s based on the open-source threat Hidden Tear, that’s quite the terror on users. Yatron gets promoted as a ‘ransomware-as-a-service,’ or Raas for short. In a nutshell, that means, it’s an infection that cyber criminals can buy the template of. Then, modify to fit their requirements. And, unleash on users, and make money. Then, they pay the people behind the Raas a percentage of their profit. That’s the gist of it. The most basic package of the Yatron Raas, comes with a ransom price that’s $300. But the price can vary, depending on which Yatron ransomware, invades your PC. You can face a ransom demand of $500 or $1500. Or, even more than that. Regardless of the price, experts advise against payment. When stuck with a ransomware menace, you face a choice. Comply or don’t. And, despite the promises of the extortionists, compliance doesn’t guarantee a positive outcome. Sure, they claim that if you follow their demands, they give you the means to remove the encryption. But all you have to go on is their word. You’re dealing with strangers, who invade your PC via trickery. Then, encrypt your files, and extort you for their decryption. Don’t forget that. These are not people, you can trust to fulfill their promises. Don’t pay them a dime.
How did I get infected with?
Yatron slithers its way into your system via deception. It resorts to all manner of tricks, and preys on your carelessness. The tool needs you to give into gullibility, haste, and distraction. That eases its covert infiltration. The ransomware’s goal is to slip by you, unnoticed. Don’t allow that. Catch it in the act of attempting to invade, and deny it entry. To do that, you have to be thorough. You must read terms and conditions, and not skip through them. You have to know what you give the green light to. Vigilance helps you to avoid any unpleasant surprises. So, take the time to be vigilant. The usual antics, infections turn to, include the following. Posing as bogus updates, hiding behind freeware, corrupted sites or torrents. And, of course, via spam email messages. The ransomware threat has plenty of tricks, it can turn to. It’s up to you to spot its attempts at infiltration. No method can prove successful, unless you provide the key ingredient. Carelessness. So, don’t. Be thorough. Take the time to read terms and conditions. Look for the fine print, and double-check everything. Caution helps you to prevent the infection’s successful invasion. Make the right choice. Choose caution over carelessness.
Why is Yatron dangerous?
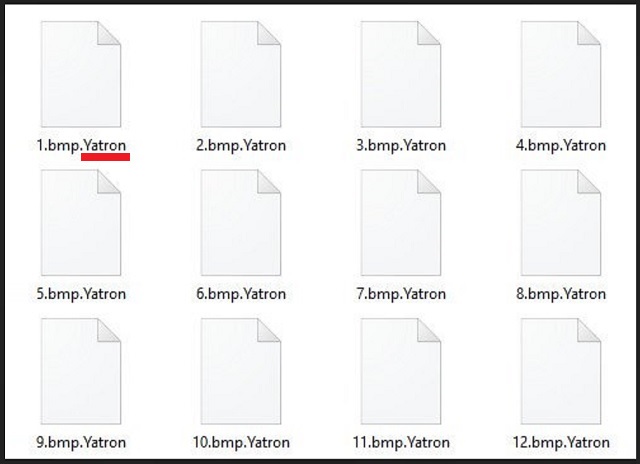
Once Yatron slithers into your system, it corrupts it. It uses cryptography algorithms to lock your data. It targets every single file, you have. To solidify its grip over your files, the tool adds the ‘.yatron‘ extension at the end of each one. If you have a song called ‘remix.mp3,’ it becomes ‘remix.mp3.yatron.’ And, once that happens, it’s inaccessible. The ransomware renders all your files unusable. And, claims you have only one way to change that. After encryption, the tool leaves you a ransom note. It’s text file, you find on your Desktop, and every folder that contains locked data. It goes by the name “Read@My.txt,” and its contents are pretty standard. The note clues you into your predicament, and provides instructions for you to follow. Don’t! Don’t leave your fate into the hands of cyber criminals. They’re unreliable, to say the least. These people care only for your money. They don’t care whether you unlock your files. Once they get you to pay them, odds are, you won’t hear from them again. Your files will remain encrypted. Even if you comply to your fullest, odds are not in your favor. Don’t forget you’re at the mercy of cyber extortionists. Compliance guarantees you nothing. Don’t waste your time, energy and money. Don’t pay the ransom.
Yatron Removal Instructions
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Yatron Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.
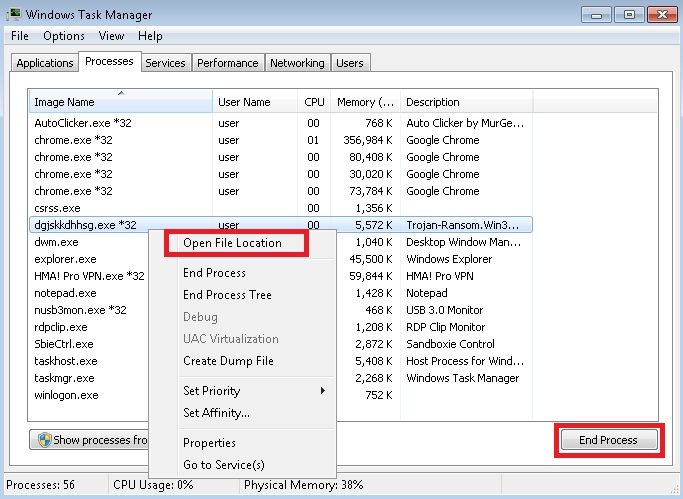
- Locate any suspicious processes associated with Yatron encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Yatron encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]
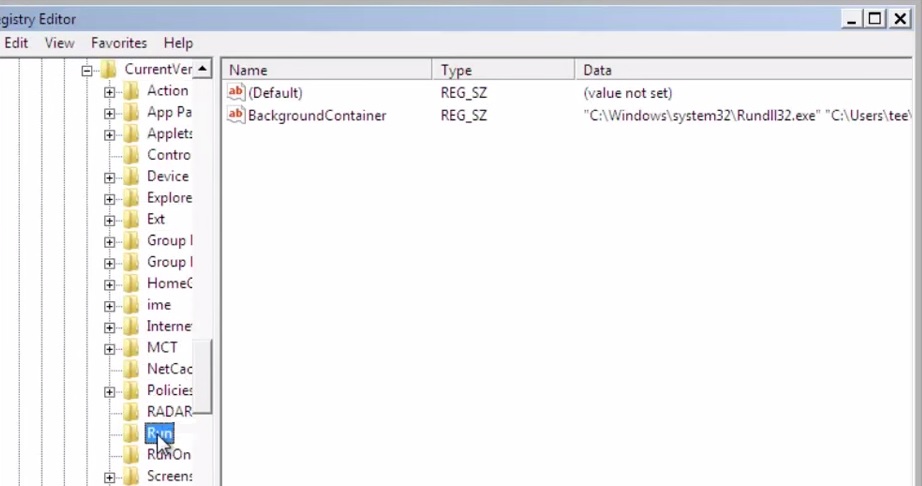
- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.
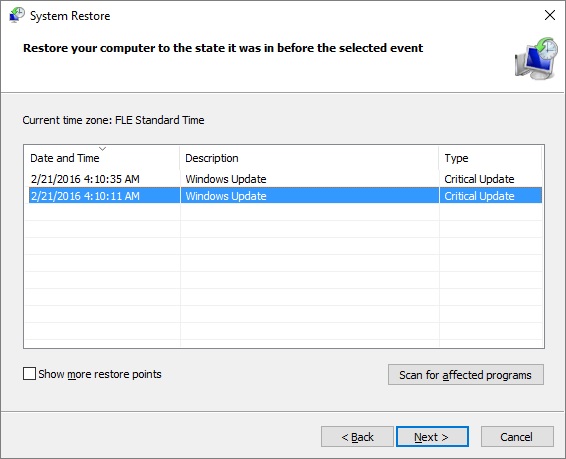
- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.


