Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove UltraCrypter Ransomware?
Reader recently start to report the following message being displayed when they boot their computer:
All you data (photos, documents, database, …) have been encrypted with a private and unique key generated for this computer.
It means that you will not be able to access your files anymore until they’re decrypted. The private key is stored in our servers and the only way to receive your key to decrypt your files is making a payment.
The payment has to be done in Bitcoin to a unique address that we generated for you, Bitcoins are a virtual currency to make online payments. If you don’t know how to get Bitcoins, you can google “How to Buy Bitcoins” and follow the instructions.
YOU ONLY HAVE 4 DAYS TO SUBMIT THE PAYMENT! When the provided time ends, the payment will increase to 5 Bitcoins. Also, if you don’t pay in 7 days, your unique kay will be destroyed and you won’t be able to recover your files anymore.
To recover your files and unlock your computer, you must send 1.2 Bitcoins (500$), to the next Bitcoin address: –
WARNING!
DO NOT TRY TO GET RID OF THIS PROGRAM YOURSELF, ANY ACTION TAKEN WILL RESULT IN DECRYPTION KEY BEING DESTROYED. YOU WILL LOSE YOUR FILES FOREVER. ONLY WAY TO KEEP YOUR FILES OS TO FOLLOW THE INSTRUCTIONS.
1. To decrypt your files you need to make pay for UltraDeCrypter and receive a private key to decrypt your files.
2. Download UltraDeCrypter to begin to decrypt your files. The link to download the program will appear here, after you pay.
3. Install the program on your computer and press the SCAN button to find all the encrypted files.
4. Please wait until the program finishes searching your files and reports the successful completion of the operation.
5. If your payment has been confirmed, you will be able to see your private key on this page.
6. Copy your private key and place it in the text box of the program, as shown in the image.
7. Please press the DECRYPT button and wait until the program finishes decrypting your files and reports the successful completion of the operation.
8. That’s all! Your files have been restored and you can use them again!
Question: How can I decrypt my files after the payment?
Answer: After the successful payment, you can download UltraDeCrypter on your personal page. We guarantee that all your files will be successfully decoded.
Question: What exactly should I specify in the field “Transaction ID”?
Answer: Specify the transaction ID you received during the Bitcoin successful purchase on the merchant’s site.
We give you the opportunity to decrypt one file completely FREE OF CHARGE!
You can be sure that the server actually operates, and after making the payment, you can decrypt all files using UltraDeCrypter
Note: The file cannot be larger than 512 kilobytes
UltraCrypter is a menacing cyber threat, which belongs to the ransomware family. And, that’s a family that you never want to cross. These infections are malicious, hazardous, and immensely damaging. They’re designed by wicked people, who cannot be trusted, which is why it should come as no surprise that the UltraCrypt tool is highly unreliable. Ransomware programs are designed to operate following a simple pattern: invade your PC, encrypt every file they come across, demand a ransom for decryption. And, if you fail to comply, the tools have various responses. Some delete files, others raise the requested ransom. The scenario varies for the different tools. When it comes to UltraCrypt, it employs both tactics. Once it has taken your data hostage and informed you of its requests if you don’t follow through on them in the given time frame, the infection doubles the ransom! And, if you attempt to remove the program yourself, it threatens to delete the key you’ll need to decrypt your files. With it lost, you won’t be able to get your data back. The ransomware clues you into all of that as soon as it’s done with the encryption process. It displays a message on your screen, which contains all of its demands and instructions on exactly how to follow through on them. And, here’s what experts advise you to do: forsake your files! Do NOT pay these people! If you pay up, your predicament will only worsen! Not only will you lose money, but you’ll also open the door to your personal and financial information to unknown individuals with hidden agendas. Needless to say, that is a terrible idea. And, remember how we stated that these people cannot be trusted? Even if you comply with their requirements, there are NO guarantees you’ll manage to decrypt your data. There are various ways they can deceive you, and NOT keep up their end of the bargain. So, accept the inevitable, and say goodbye to your files. Choose your privacy over your pictures and videos. It’s a hard choice, but it’s the right one.
How did I get infected with?
UltraCrypter is a deceitful and sneaky tool. It’s so skilled in the arts of slyness and subtlety that it manages to invade your computer, and remain hidden until it decides it’s time to clue you into its existence. That’s right. Not only does the tool gain entry but it also keeps you oblivious to it. And, how do you suppose it accomplishes that? Well, you provide the key ingredient – carelessness. Cyber threats like UltraCrypter use it to slither in undetected, usually as you’re installing a tool or an update. Yes, ransomware tends to turn to the old but gold means of infiltration as they’ve proven their worth over time. That can include hiding behind freeware, corrupted links, or sites or pretending to be a fake update, like Adobe Flash Player or Java. However, UltraCrypter’s most commonly used method, to dupe you into allowing it into your system, is spam email attachments. The infection is spread via an attachment made to look like a letter by an official institution or company. Fall for it, and you’re stuck with ransomware. That’s why it’s crucial to take everything with a grain of salt. Don’t give into gullibility and distraction, and don’t rush! Remember that sometimes even a little extra attention can save you a ton of troubles.

Why is UltraCrypter dangerous?
Once UltraCrypter slithers into your computer, it hardly wastes time. The infection goes to work and encrypts everything you have stored on your PC. And, we do mean everything. You better believe the tool leaves no stone unturned as it locks every picture, video, document, music file, etc. And, when it’s done, it supplies you with its requirements. In a nutshell, your data is now its captive, and if you wish to release it, you must pay a ransom. UltraCrypter uses an asymmetric encryption algorithm to get a hold of everything. And, it generates two keys. One is public (RSA-2048), and one is private (AES CBC-256) are generated. The private key is stored on the remote servers, which are controlled by the hackers. Naturally, that’s the one you want are have to pay for. The ransom amount is 1.2 Bitcoins, which is equivalent to around $644. That’s no small amount! But wait until you read the fine print. On the note, which the tool displays to inform you of your predicament, it’s clearly specified that you have four days to complete the transfer. If for some reason, you do not pay up, there are consequences. Once the given four days end, the requested ransom will grow in amount. It can reach over $1200 or even more! And, if you still refuse to pay after seven days time, your unique decryption key is destroyed. It may be a scenario, which you understandably wish to avoid, but understand this: even if you comply with every demand the tool has made, you could still end up with no access to your files, less money, and your personal and financial details in the hands of strangers. Yes, the people behind the ransomware infection cannot be trusted to keep their end of the deal. So, why do it? As harsh as it may seem, the best course of action you can take is let go of your data. It’s not worth your privacy.
UltraCrypter Removal Instructions
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover UltraCrypter Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.
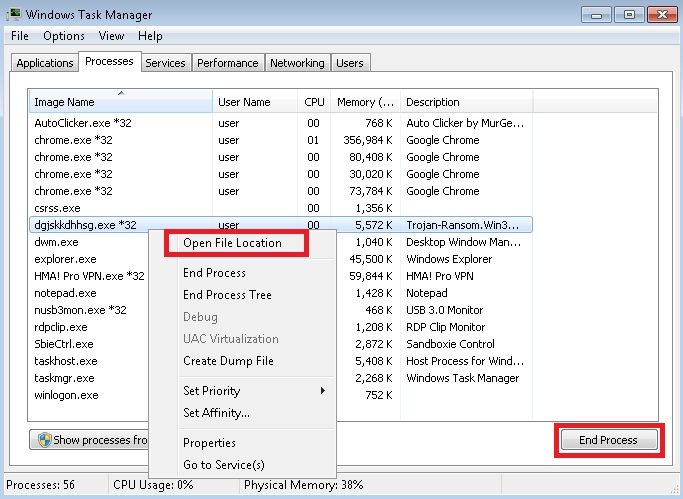
- Locate any suspicious processes associated with UltraCrypter encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate UltraCrypter encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]
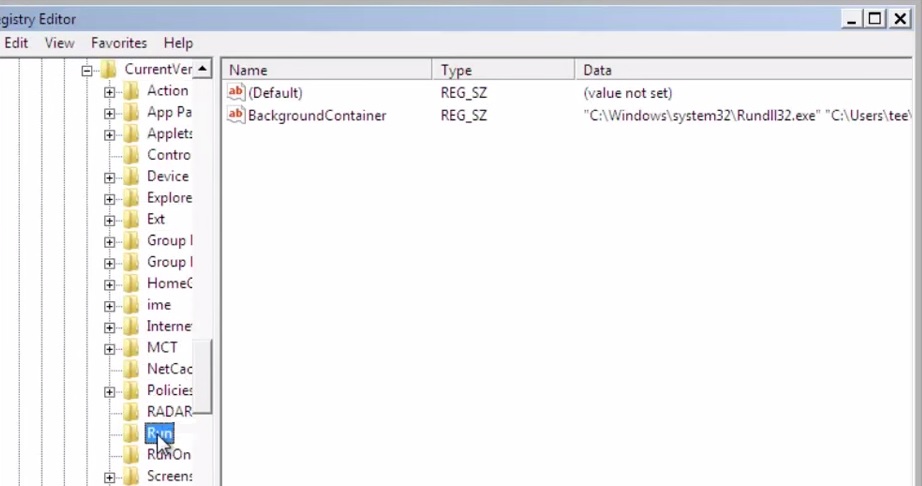
- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
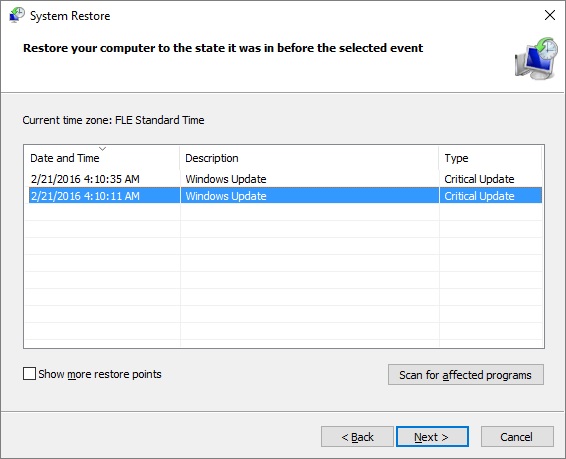
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.
- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.



