Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
What is Zepto File Ransomware and How to Remove The Virus?
This article is created to help you remove Zepto file virus. The Zepto Removal instructions will work on all Microsoft Windows Operating systems. Just a couple of days ago we came across a brand new infection. The problem is, we’re talking about ransomware. This is one of the most destructive types of viruses currently on the Web. In fact, some researchers go as far as to say ransomware IS the absolute worst thing you could possibly install. Ransomware relies on your anxiety and despair in order to extort money from you. By using a strong encrypting algorithm, the parasite locks all your personal files and makes them inaccessible. Thus, all your private information becomes useless. You now have on board a virulent, aggressive and problematic PC virus. It’s quite obvious you need to take action on the spot. As already mentioned, you’ve fallen victim to a recently developed cyber pest. It is actually a new version of the infamous Locky Ransomware and it’s just as dreaded as Locky. The main difference between the two is the file extension the parasite adds. In this case, you’ll notice a .Zepto appendix. Just like Locky does, this program renames your data. It adds a unique combination of 16 symbols (consisting of both letters and numbers) to your files. This is your ID. In order to locate your personal data, the parasite first scans your machine.
Thanks to this thorough scan, the virus finds pictures, music, MS Office documents, videos, etc. Ransomware takes down a huge variety of file formats so nothing you’ve stored on your PC is safe. It encrypts .mp3, .mp4, .jpg, .jpeg, .pdf, .ppt, .gif, .txt, .doc, .docx files and many more. As you could imagine, there might be some immensely important information among these files. Unfortunately, though, this problem is yours and yours only. Hackers have absolutely no reason to take care of your valuable data. Quite the opposite; crooks rely on the fact you’ll have something important encrypted. That is how you get scammed. While locking your files, the parasite also drops detailed payment instructions. According to these ransom messages, you have to pay a certain sum of money in Bitcoin to restore your files. Bitcoin is a popular online currency and usually the sum required is a hefty one. The ransom note emphasizes that the only way to regain access to your data is by following hackers’ instructions. What do you think about it? It is worth it to give your money away waiting for a miraculous solution? Is it worth it to negotiate with greedy and dishonest cyber criminals? Don’t be gullible. Ransomware was only developed to blackmail you.
How did I get infected with?
Spam message from unknown/known senders, spam email-attachments, malicious torrents, dangerous websites, flash player vulnerabilities, etc. The list of potential infiltration methods is quite impressive. More often that not, the virus pretends to be a legitimate email from a shipping company, or a job application. This way it tricks you into opening the infected email. Next time you notice something untrustworthy in your inbox, don’t hesitate to delete it. Also, stay away from unreliable and illegitimate pages. In addition, ransomware-type infections travel the Web as fake software updates. Another technique is freeware/shareware bundling. You see, this nuisance has many options to choose from. It’s your responsibility to prevent all of them. Take your time when installing programs and watch out for malware beforehand. There’s no such thing as being too cautious and careful online. Thus, your cyber safety depends solely on your actions.
Why is Zepto dangerous?
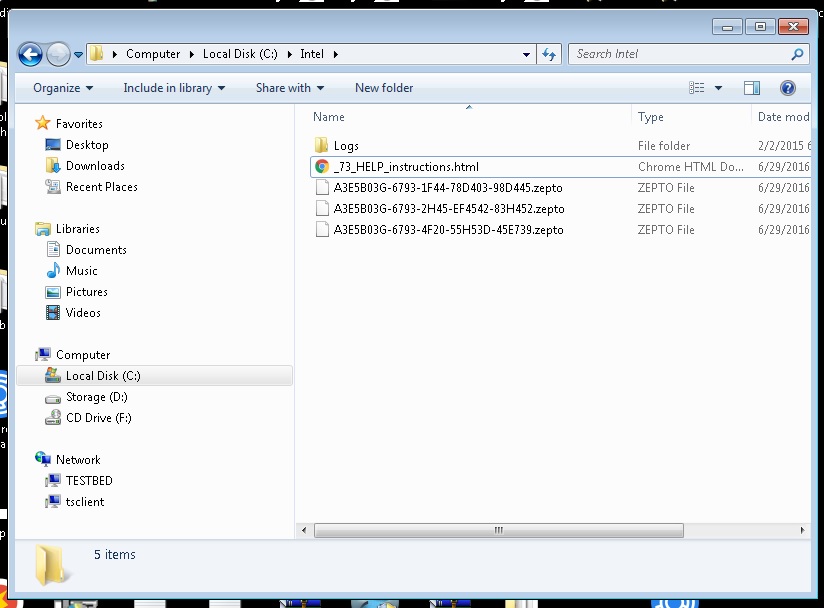
The virus creates .txt and. html files which contain its ransom message. The naming format is in the form of [first_8_hexadecimal_chars_of_id]-[next_4_hexadecimal_chars_of_id]-[next_4_hexadecimal_chars_of_id]-[4_hexadecimal_chars]-[12_hexadecimal_chars].zepto.
It may also modify your desktop wallpaper. Now you’re being constantly reminded that your files are held hostage and you need to pay a ransom to set them free. You see, many PC users would panic seeing these sudden modifications. The .Zepto file extension appears out of nowhere and you can no longer use your infected data. Quite nerve-wrecking, isn’t it? However anxious you might be, keep in mind this is all a cheap trick aiming at your bank account. Paying the money demanded guarantees you nothing. What’s even worse is that, if you pay, hackers get access to your private information. Crooks would not hesitate before they use your own data against you so make no mistake. Restrain yourself from contacting hackers. This simply cannot end well. The virus promises a decryption key in exchange for your bitcoins. That means the absolute last thing you do should be paying the ransom. Instead, get rid of the parasite and don’t sponsor hackers’ malicious business. To delete this pest manually, please follow the detailed removal guide you will find down below.
Zepto Removal Instructions
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Identify and Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Zepto Encrypted Files
WARNING! Stopping the wrong file or deleting the wrong registry key may damage your system irreversibly.
If you are feeling not technical enough you may use Spyhunter professional Zepto Removal Tool. However, only the Scanner is FREE, in order to remove the ZEPTO Files virus completely you need to purchase full version. >>Download SpyHunter – a professional .Zepto scanner and remover.
>>Download SpyHunter – a professional .Zepto scanner and remover.
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware.
- Before you kill the process, type the name on a text document for later reference and to be able to delete it.
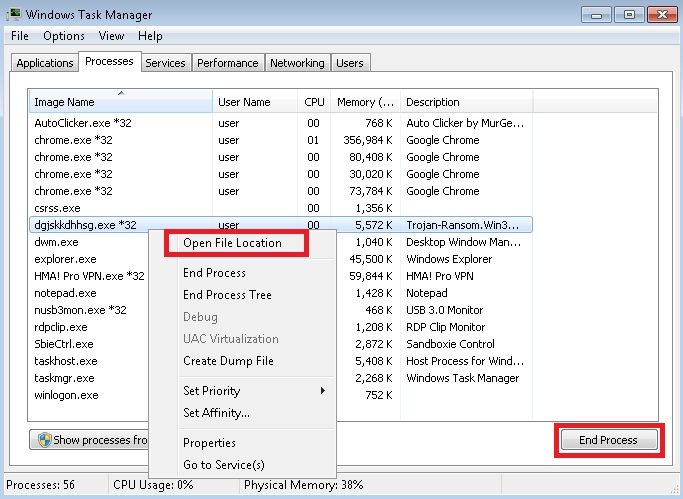
- Locate any suspicious processes associated with Zepto encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
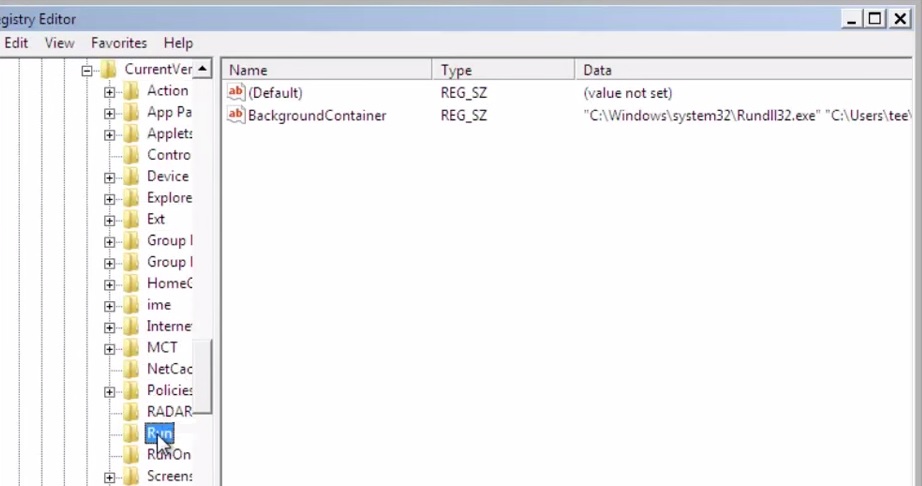
STEP 3: Locate Zepto encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
HKCU\Control Panel\Desktop\SCRNSAVE.EXE “%AppData%\[random].exe”
HKCU\Software\Microsoft\Command Processor\AutoRun “%AppData%\[random].exe”
HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run “%AppData%\[random].exe”
HKCU\Software\Microsoft\Windows\CurrentVersion\Run\[random] “%AppData%\\[random].exe”
HKCU\Software\Microsoft\Windows\CurrentVersion\RunOnce\[random] “%AppData%\\[random].exe”
- and delete the display Name: [RANDOM]
- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
Navigate to %windir%/system32/Drivers/etc/host
If you are hacked, there will be foreign IPs addresses connected to you at the bottom. Take a look below:
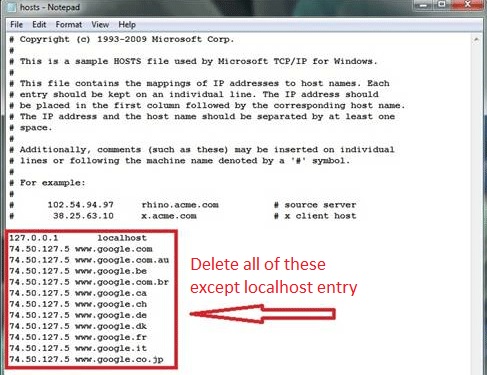
If you are uncertain about the IPs below “Localhost” contact us in out google+ profile and we will try to help you.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.
- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
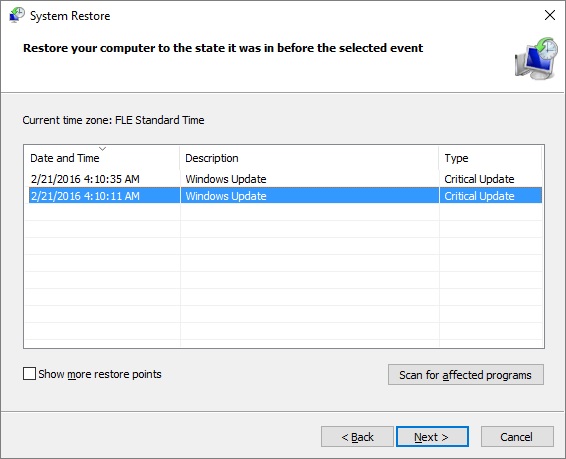
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover.
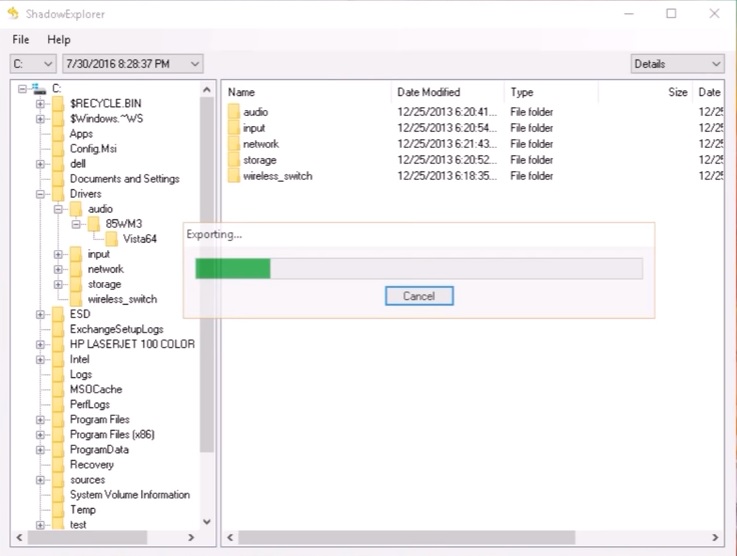
- Right click on any file you want to restore and click Export on it.

