Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Asasin Ransomware?
Readers recently started to report the following message being displayed when they boot their computer:
Your device has been invaded by a malware version called .Asasin Virus. All the files on your computer and to which you have to access on a daily basis have been encrypted. In case you want to recover your access to all such data, it is obligatory that you pay a certain amount in ransom.
If your files have been encrypted and renamed, you’re dealing with ransomware. Today’s article is about one of the latest additions to the ransomware family. It adds the .Asasin extension to the target files thus indicating they are locked. Note that you’re stuck with perhaps the most dangerous parasite out there. Ransomware is no threat to be taken lightly so you’re in for trouble. The sooner you manage to get rid of the infection, the better. Its trickery begins immediately after installation. For starters, this program scans your machine thoroughly. By doing so, it locates the exact files that is about to encrypt later. Needless to say, ransomware always finds what it searches for. The problem is that all your private files are about to fall victims to the parasite. That includes photos, music, videos, various documents. Ransomware modifies a huge percentage of your information. Do you store important files on your computer? If you do, make sure you also have backup copies. This will easily save you the headache if you cross paths with ransomware again. Remember, when it comes to ransomware, you have to think in advance. Take care of your precious files. Once the parasite locates your data, encryption begins. The ransomware uses a complicated cipher and successfully locks all your files. That means you’re being denied access to your own information. And if that sounds unfair, just wait till you learn what follows. Ransomware adds a malicious file extension to the data it has encrypted. In this case, the appendix is .Asasin. This is it. You’re no longer able to open any of your files, regardless of how important they are. The parasite locks all your favorite pictures, funny videos and work-related documents. It aims at getting you to panic because the scam is just getting started. The ransomware drops detailed payment instructions on your PC screen. It also adds these ransom notes to every folder that contains encrypted files. The bottom line is, you constantly come across its ransom messages. As you could imagine, that is nothing but a cheap trickery hackers use to steal your money. According to the ransom notes, you need to buy a decryptor to free your files. Hackers offer you a deal that will involve you in a cyber fraud and cause you damage. Therefore, the very last thing you should do is follow crooks’ instructions.
How did I get infected with?
Spam emails and messages are often corrupted. Unless you keep an eye out for malware, it’s very easy to compromise your safety. We recommend that you delete all suspicious-looking emails or messages you receive. This is one extremely popular method hackers use to spread infections online. Put your security first and stay away from anything untrustworthy you may find in your inbox. Even if a certain spam email appears to be harmless, be careful. It isn’t uncommon for ransomware to pretend to be a job application, for example. Watch out for emails from some shipping company as well. In addition, these parasites use exploit kits and freeware/shareware bundles to get spread online. Another famous trick involves fake torrents as well as bogus software updates and corrupted third-party pop-ups. Avoid installing unverified programs and don’t trust illegitimate websites. Protecting your device from viruses is your responsibility so don’t be negligent.

Why is Asasin dangerous?
The ransomware successfully holds your files hostage. It then attempts to trick you into buying a decryption key so you could restore your data. Bear in mind that you’d be making negotiations with greedy cyber criminals. Those are the very people who locked your information in the first place. They really shouldn’t be rewarded for that. Keep your Bitcoins and ignore the parasite’s nerve-racking ransom notes. You certainly can’t trust hackers to keep their end of the bargain so don’t let them scam you. If you believe the ransomware’s messages, you’ll fall right into the trap and waste money. You have no reason whatsoever to expect crooks to provide you the decryptor they promised. On the other hand, you have plenty of reasons to delete the devious ransomware ASAP. Please follow our detailed manual removal guide down below.
Asasin Removal Instructions
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Asasin Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.
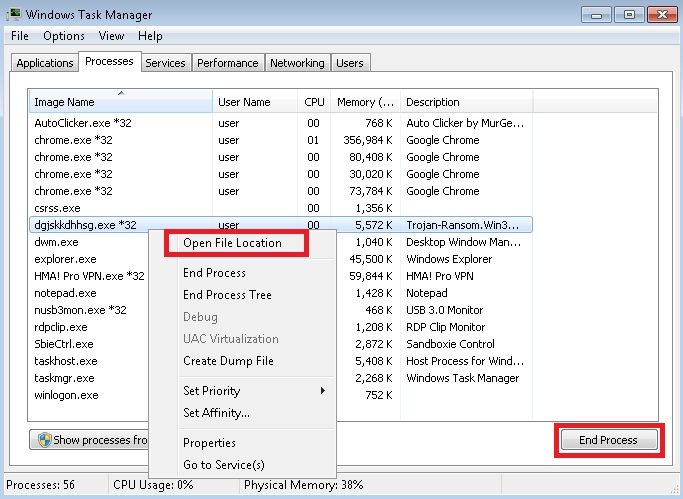
- Locate any suspicious processes associated with Asasin encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Asasin encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]
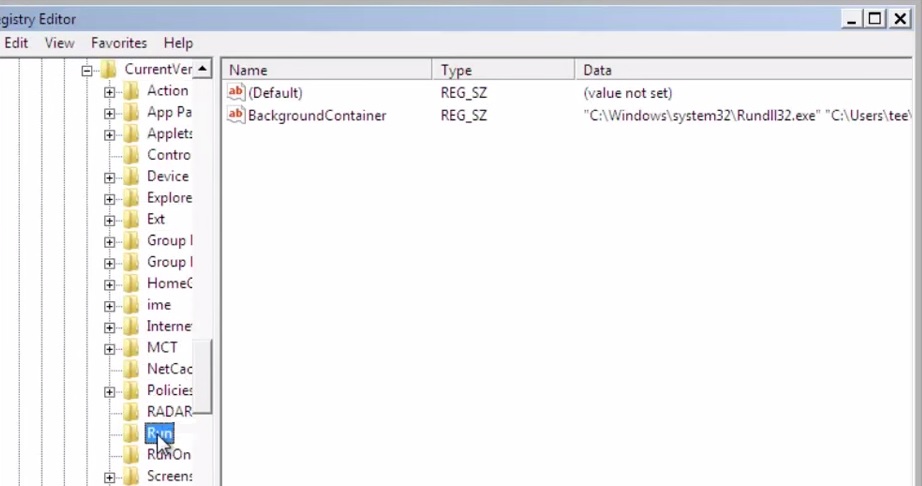
- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
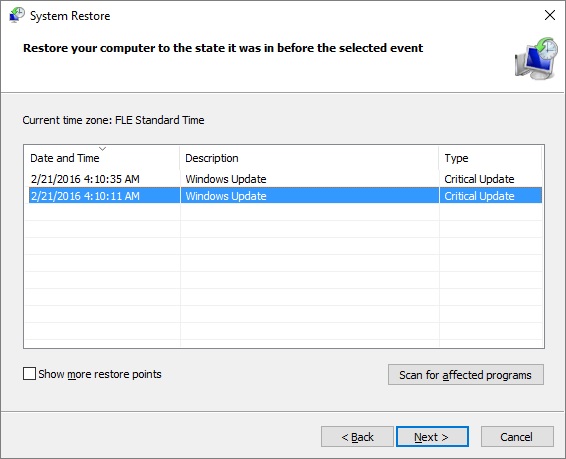
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.
- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.



