Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.

Computer Virus Using Inaudible Sound Waves to Transmit Data
Do you think that if your computer is not connected to a network and you do not use USB sticks, CDs, DVDs, then you are safe against hackers and malware – you are wrong!
The story about the mysterious BadBIOS virus, a malware not using conventional means of transfer, was introduced a few weeks ago by the security consultant Dragos Ruiu. He noticed something highly unusual: his MacBook Air, on which he had just installed a fresh copy of OS X, spontaneously updated the firmware that helps it boot. Even more puzzling, when Ruiu then tried to boot the machine off a CD ROM, he could not. He also found that the computer can delete data and make configuration changes with no prompting whatsoever. He didn’t know it then, but that odd firmware update would become a high-stakes malware mystery that would consume most of his waking hours.
Further investigation, revealed that the number of computers experiencing similar behavior start to raise, the systems include multiple variants of Windows and Linux. Ruiu words were “Okay, we’re totally owned” and “We have to erase all our systems and start from scratch”. After many hours of installation and reconfiguration of the affected systems – the problem didn’t disappear. He thought that USB sticks were the infection vector and the virus is residing in the computer’s Basic Input/Output System (BIOS), Unified Extensible Firmware Interface (UEFI), and thus the malware can infect a wide variety of platforms, avoid common forms of detection, and survive the attempts to be removed.
The story gets even stranger when Ruiu posted another theory that sounds like something from a post-apocalyptic movie: “badBIOS,” as he named the malware, has the ability to use high-frequency transmissions passed between computer speakers and microphones to close airgaps.
Just imagine, a cyber-attack using high-frequency sound waves to infect machines, where stolen data also can be transferred back to attacker without a network connection. Sounds very terrifying, isn’t it ? Some people said he was crazy.
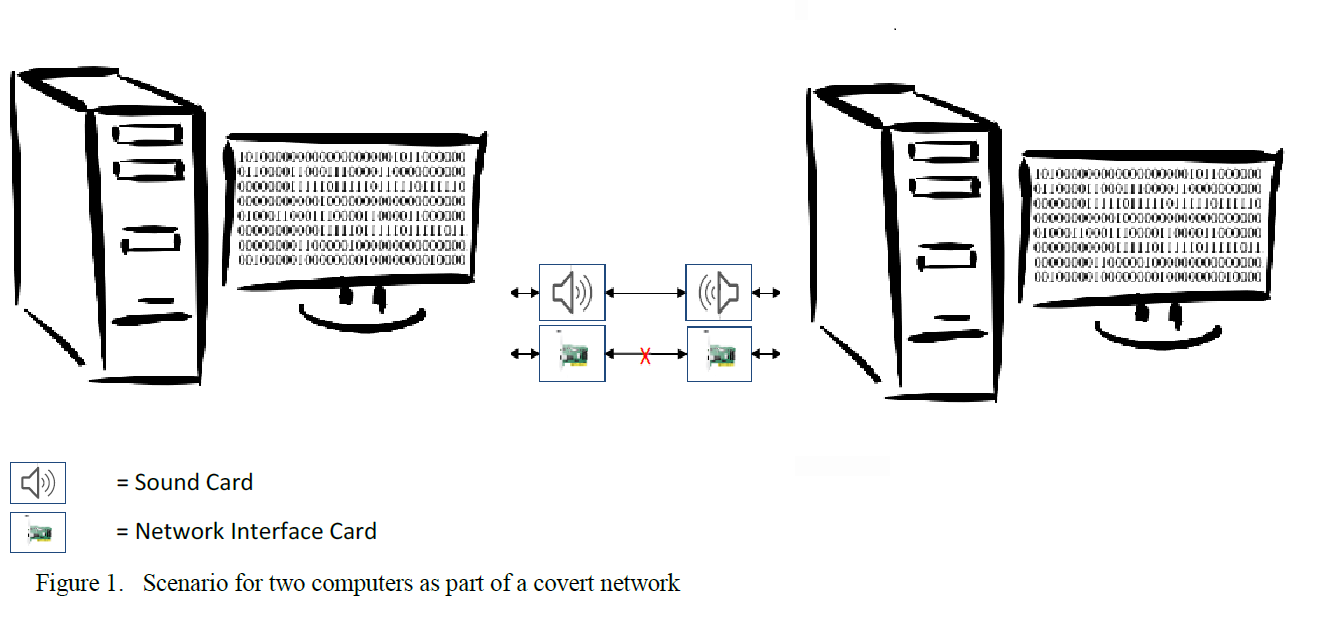
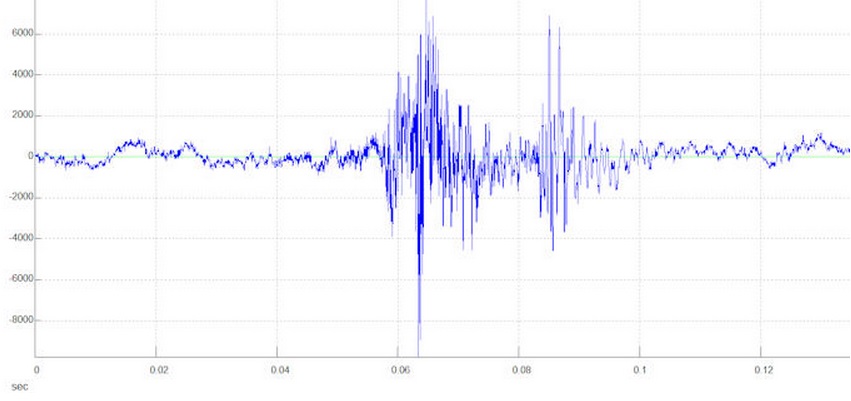
Now, a new shocking story is rising. Michael Hanspach and Michael Goetz – German Scientists have developed a proof of concept that Hackers will be able to utilize (or are already utilizing) Inaudible Audio signals to transfer data using Inaudible Audio signals. They have published a paper on how malware can be designed to cross the air gap by transmitting information through speakers and recording it via microphone.
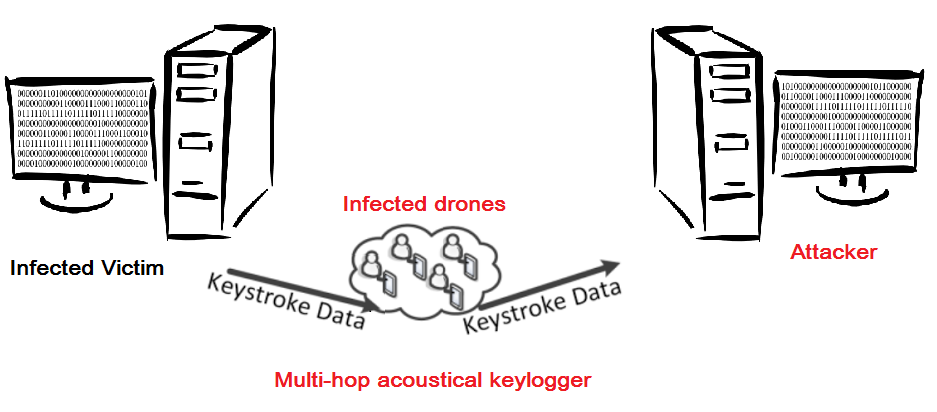
In an improvised hacking scenario the infected victim sends all recorded keystrokes to the covert acoustical mesh network. Infected drones forward the keystroke information inside the covert network till the attacker is reached, who is now able to read the current keyboard input of the infected victim from a distant place.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
In another scenario, the scientist used sound to send keystroke information to a network-connected computer, which then sends the information to an attacker via email. While this does not prove what Dragos Ruiu’s badBIOS virus claims, but it proves that even if the system is disconnected from any network, it could be still vulnerable to attacks. The data transfer was at 20 bits per second only (that is very low), but it is still enough to transfer your passwords or credit card number to the hacker in seconds.
Even though this is not an actual attack and nothing in the paper suggests that you can compromise a computer via its microphone. The danger is laying in that infected computers might not be detectable by anything as they don’t communicate on via network card. Also, they may be able to slip past security appliances onto the internet itself by communicating to nearby computers on a different network.
Suggested countermeasures to protect against such malware is:
- Switching off the audio input and output devices from the system.
- Employ audio filtering that blocks high-frequency ranges.
- Development and usage of an Audio Intrusion Detection Guard.
Let’s wait and see how Antivirus companies will handle these threats to protect home users.