Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
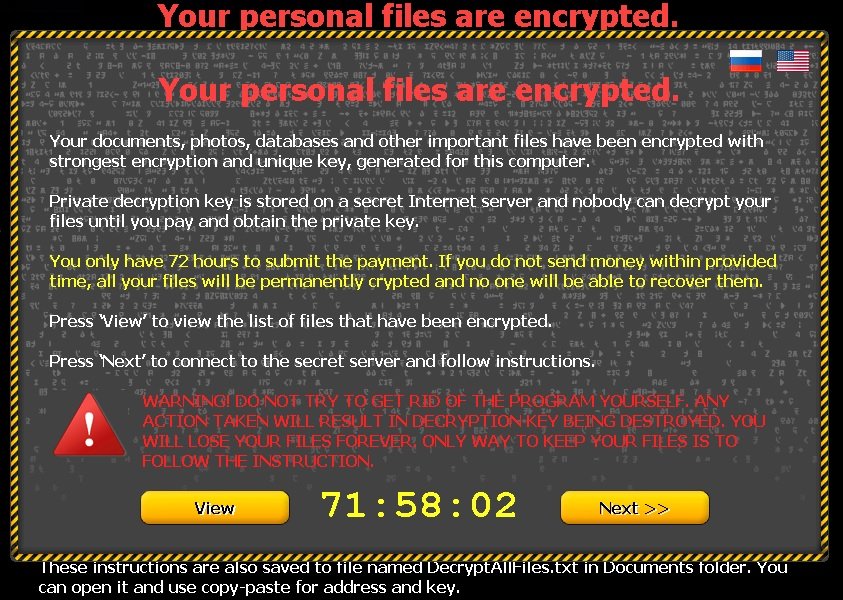
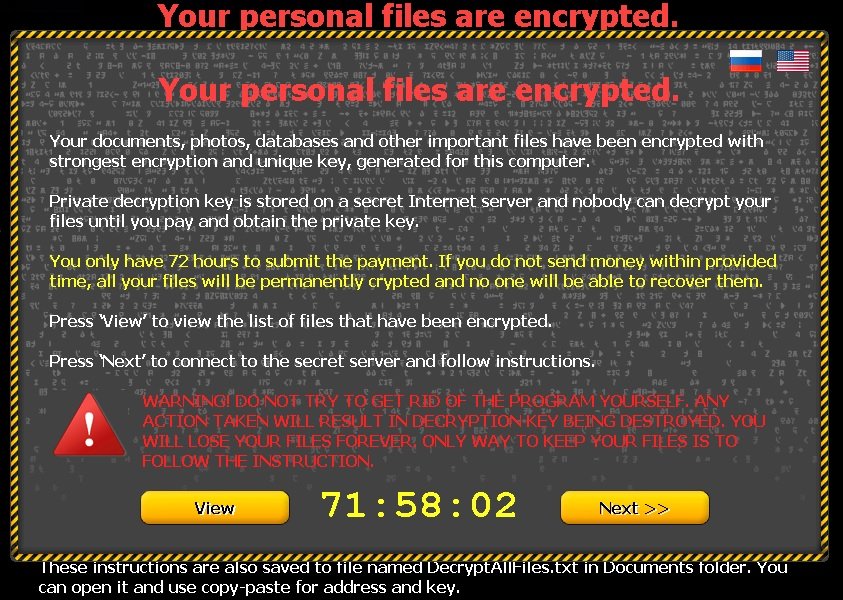
If you are seeing “Your personal files are encrypted” message – you are infected with CTB Locker (Critoni) Ransomware!
CTB Locker is an infection you do not want to find on your computer. Ever. It is classified as ransomware and is part of the Crypto Ransomware family. CTB Locker jeopardizes all the files you have stored on your PC. It’s malware that puts you in a corner by “kidnapping” all of your files and forcing you to pay ransom if you ever want to have access to them again. Unfortunately, paying the ransom doesn’t always work, so even if you do exactly what CTB-Locker wants, you still might end up losing everything on your PC. As you might have guessed already, it is a definite must to delete this program as soon as possible, even though it’s easier said than done. Not many people have the stomach to put every single one of their files on the line, as it is quite the gamble, and odds are in favour of you ultimately losing them.
How did I get infected with Critoni?
Like most malware, CBT Locker resorts to trickery in order to access your system. There are many ways of infiltration. Some of the most common ones include compromised web links, malicious websites, spam email messages, false system upgrades, and freeware downloads from suspicious sources. CBT Locker usually invades your system with the help of a Trojan. Once the Trojan has made its way to your PC, it installs the ransomware infection and then it goes to work. CBT Locker encrypts all of your files – photos, music, documents, everything. Bear in mind that once the Trojan has installed the ransomware, it just sits back and watches, as CBT Locker wreaks havoc.
Why is Critoni Dangerous?
Once CTB-Locker is finished with encrypting your files, it displays a message on your desktop that replaces your wallpaper and all of your icons, and makes sure you only have eyes for it. The message states that if you want your files decrypted, you have to pay ransom within 72 hours. If you restart your PC, the message will disappear and you’ll have access to your Task Manager and see your icons and Task bar again, but your files will still remain encrypted. Even though, the ransom differs, CTB-Locker most commonly asks you to buy bitcoins, worth approximately 24 USD via an online transaction. If you choose to pay the “kidnappers” off, you have to download the Tor Internet browser. Once you have the browser set up, the next thing you have to do is enter a private key and then go through with the payment. But even then there are no guarantees that your files will be decrypted. All that’s left to do after the payment has been made, is to delete the Trojan from your system as soon as you possibly can, in order to avoid appearances from the ransomware in the future.
How to Remove CTB-Locker?
from Windows 7 (Win 8 instructions are further below)
- Make sure you do not have any floppy disks, CDs, and DVDs inserted in your infected computer
- Restart the computer
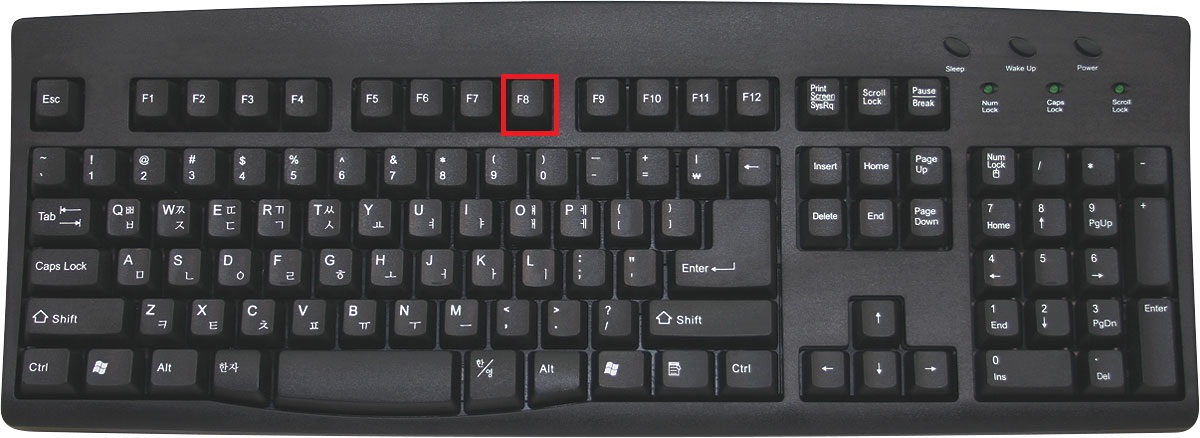
- When you see a table, start tapping the F8 key every second until you enter the Advanced Boot Options
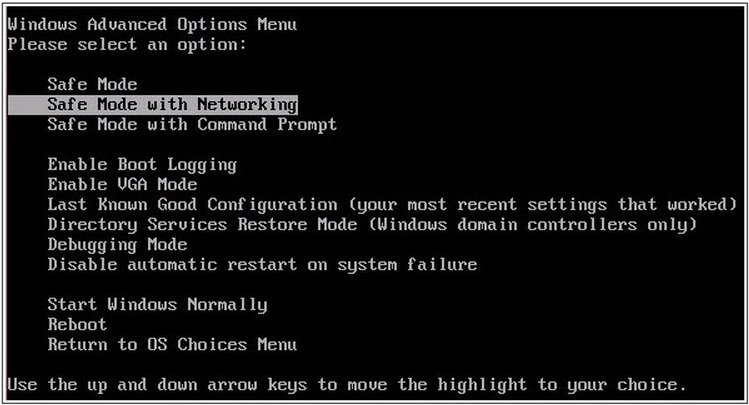
- in the Advanced Boot Options screen, use the arrow keys to highlight Safe Mode with Networking , and then press ENTER.
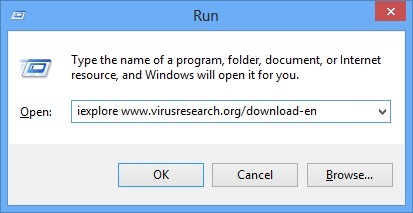
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.

- A dialog box should open. Type iexplore www.virusresearch.org/download-en
- your Internet Explorer will open and a professional scanner will start downloading
- Follow the instruction and use the professional malware removal tool to detect the files of the virus.
- After performing a full scan you will be asked to register the software. You can do that or perform a manual removal as shown in step 2
from Windows 8
Start Your Computer into Safe Mode with Networking
- Make sure you do not have any floppy disks, CDs, and DVDs inserted in your computer
- Move the mouse to the upper right corner until the windows 8 charm menu appears
- Click on the magnifying glass
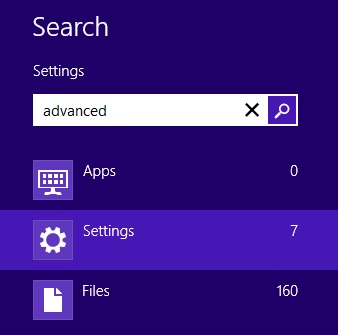
- select Settings
- in the search box type Advanced
- On the left the following should appear
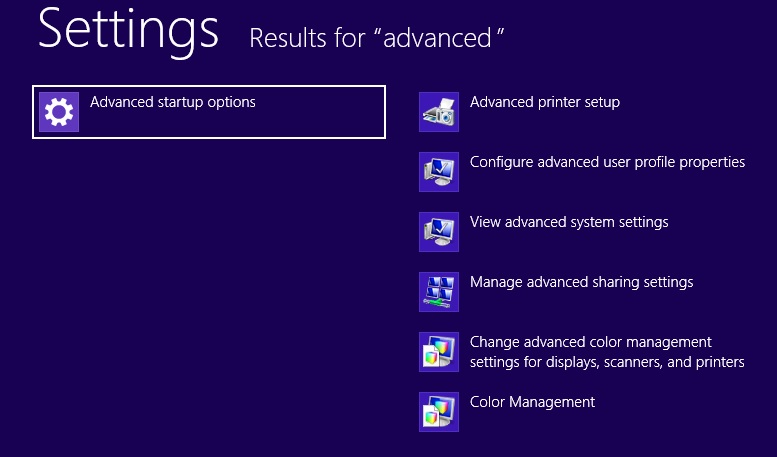
- Click on Advanced Startup Options
- Scroll down a little bit and click on Restart Now
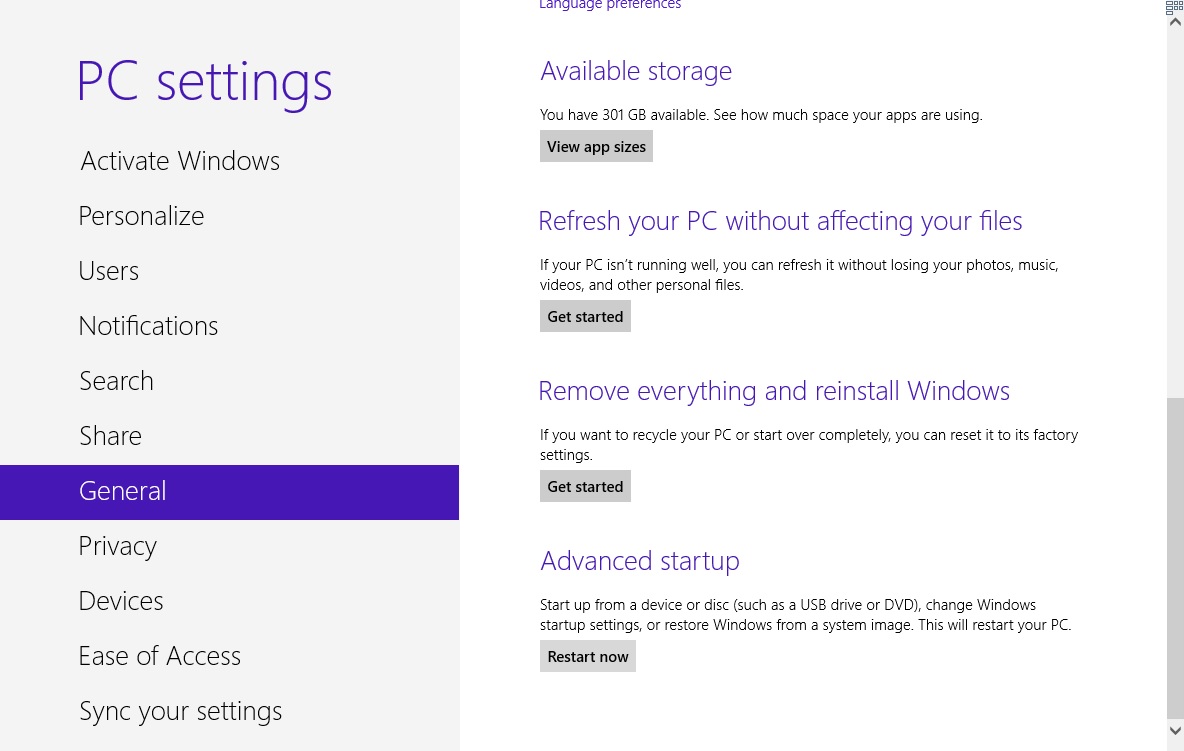
- Click on Troubleshoot
- Then Advanced options

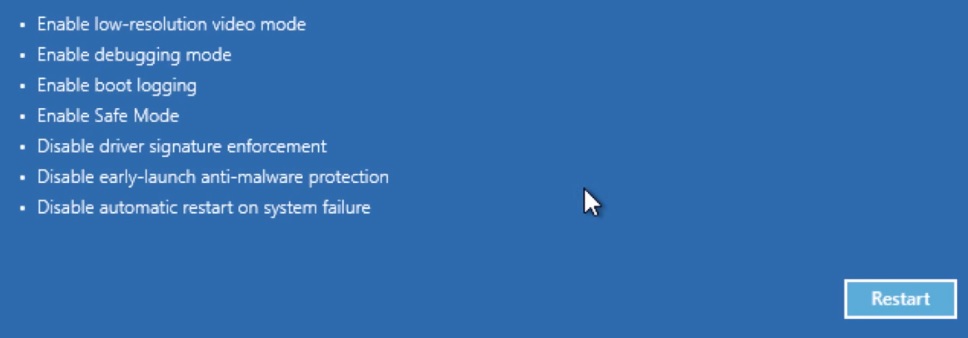
- Then Startup settings

- Then Restart
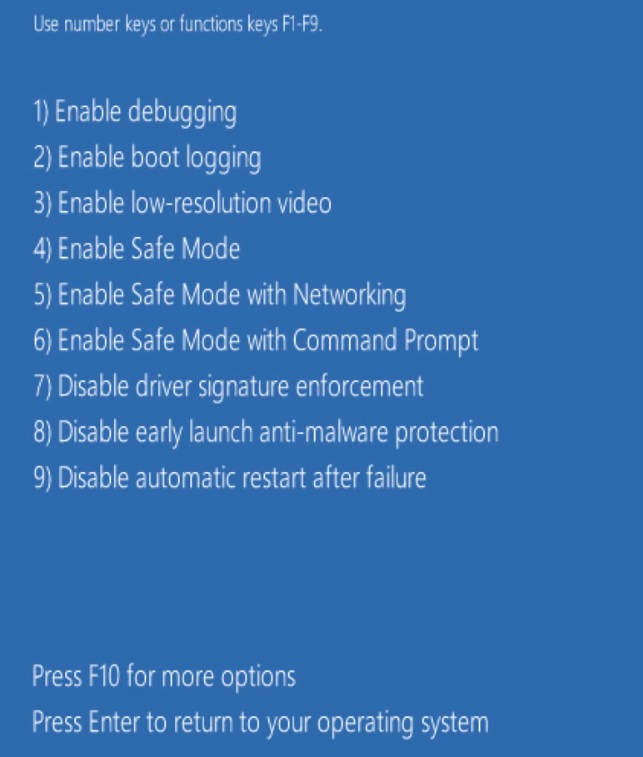
- When you see this screen press F5 – Enable Safe Mode with Networking
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.

- A dialog box should open. Type iexplore www.virusresearch.org/download-en
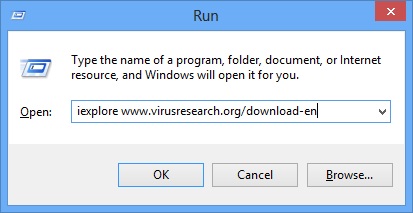
- Internet Explorer will open and a professional scanner will start downloading
- Follow the instruction and use the professional malware removal tool to detect the files of the virus.
- After performing a full scan you will be asked to register the software. You can do that or perform a manual removal.
- To perform Manual removal you need to follow the steps below.
STEP 2: Locate the virus start-up point
Simultaneously press the Windows Logo Button and then “R” to open the Run Command
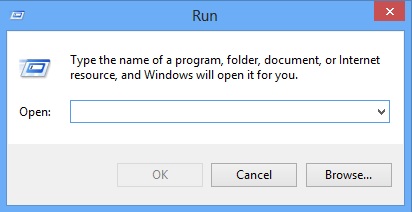
Type “taskschd.msc” in the box to open your Task Scheduler
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
After that, locate and remove the entries of the ransomware as shown below .
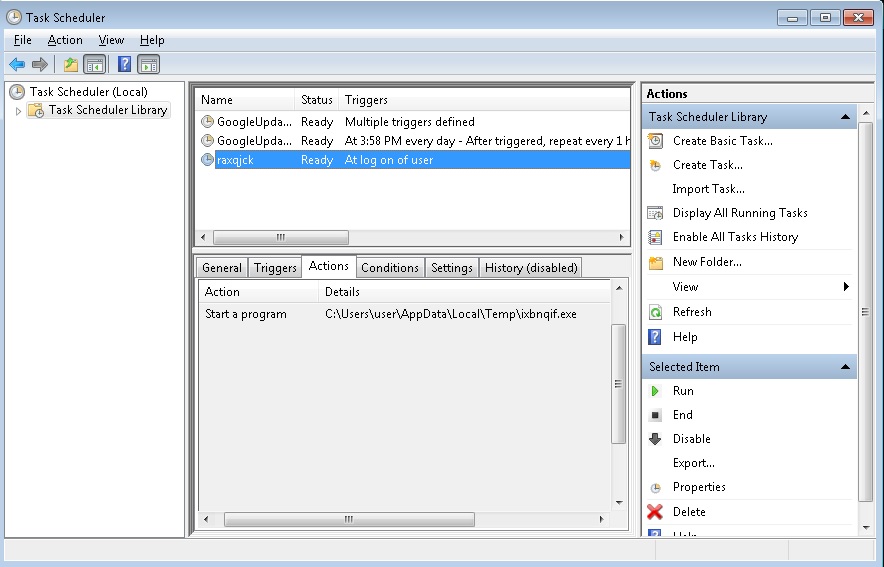
Delete the scheduled task and the file it is pointing at. Please not that the file name is random and yours might be different.
Restart Windows.
STEP 3: Restore Encrypted Files
There are several methods you can use, however nothing is guaranteed.
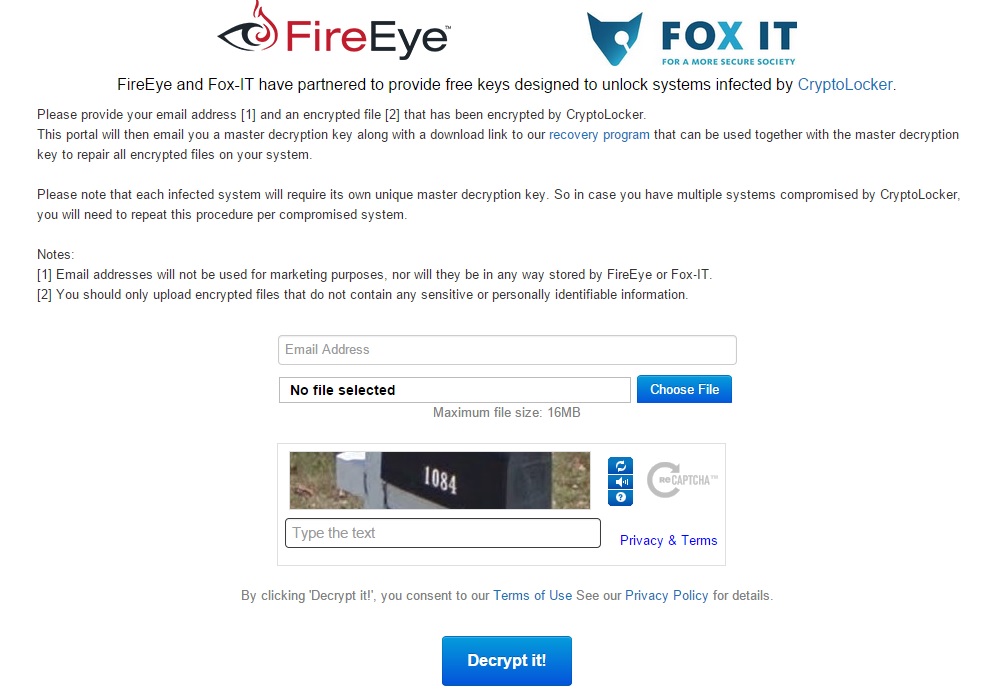
Method 1 – decrypt the encrypted files:
Method 2 – recover the encrypted files by hand:
You can try to use the built in feature of Windows called System Restore. By default the system restore feature is automatically turned on. Windows creates shadow copy snapshots that contain older copies since the system restore was performed. These snapshots will let us to recover any previous version of your file, although it will not be the latest one, still you can recover some important information. Please note, that Shadow Volume Copies are only available with Windows XP SP2, Vista, Windows 7 and Windows 8.
Method 3 – partially restore the encrypted files by using Microsoft Office junk files:
Basically you need to show your hidden files. The fastest way to do that is:
- Open Folder Options by clicking the Start button .
- In the search box type “FOLDER OPTIONS”.
- Select View TAB
- Under Advanced settings, find Show hidden files and folders and select it and then click OK.
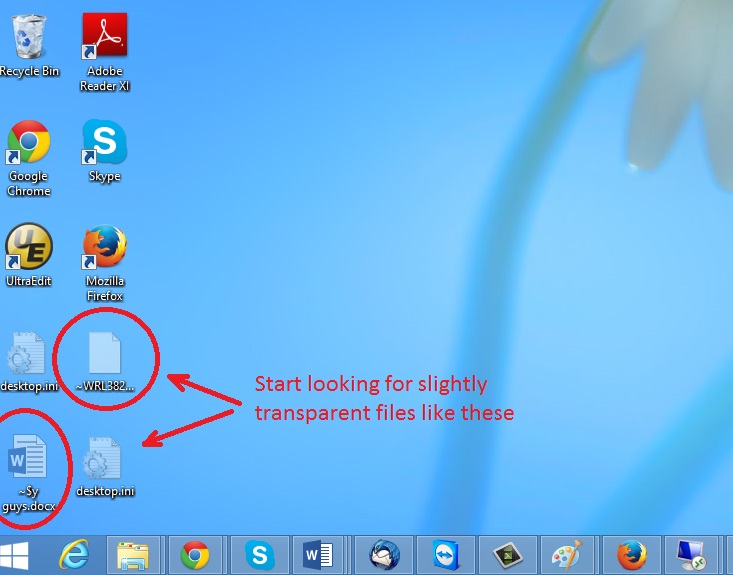
In the picture above I marked two hidden files. You are interested in every file that looks like ~WRL382.tmp This is actually a Microsoft office junk file that contains the previous version of the Word document itself. The Cryptowall parasite will not encrypt these files. The name of the file will be unknown, but you can recover a lot of lost documents using this method. This can be utilized for Microsoft Word and Microsoft Excel. In addition you can try to match the file sizes in order to figure out what is what and eventually you can restore a slightly older original document. In the picture on the left there is another method you can locate the files in question.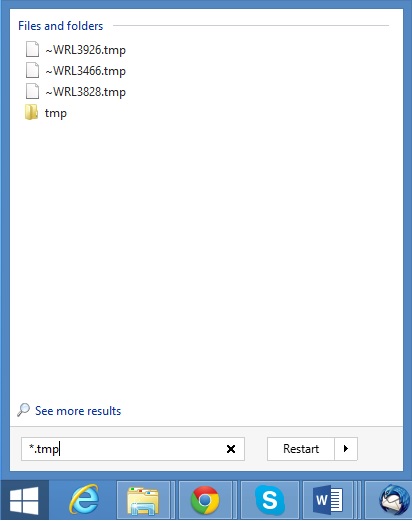 All you have to do is to hit the start button and type *.tmp. You will be presented a list of all the temp files located in your computer. The next thing is to open them one by one with Microsoft Word/Excel and recover the lost information, by saving it to another place. You can do that, by opening a new instance of MS Word/Excel, trough the file menu select open and then navigate to the location of the TMP file.
All you have to do is to hit the start button and type *.tmp. You will be presented a list of all the temp files located in your computer. The next thing is to open them one by one with Microsoft Word/Excel and recover the lost information, by saving it to another place. You can do that, by opening a new instance of MS Word/Excel, trough the file menu select open and then navigate to the location of the TMP file.