Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove X3M Ransomware?
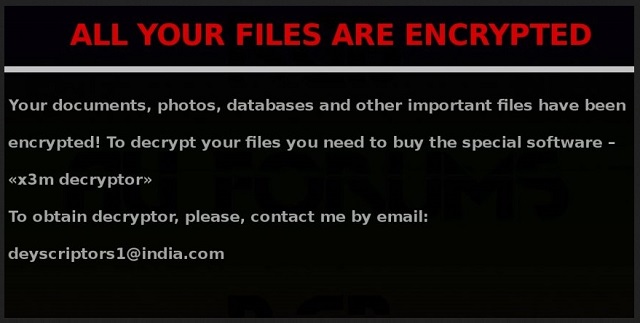
Readers recently started to report the following message being displayed when they boot their computer:
Your files are encrypted!
Your personal ID
[random characters]
Your documents, photos, databases, save games and other important data has been encrypted.
Data recovery is required decipher
To get the interpreter should send to deyscriptors24@india.com In a message write your personal identifier (you can find it in the beginning of this document).
next, you need to pay for the interpreter. In a response letter you will receive the address of Bitcoin-wallet to which you want perform the transfer of funds in the amount of 0.8 bitcoin.
The category with the most horrendous cyber threats is, undoubtedly, that of ransomware. Ransomware programs are an utter cyber plague. Well, they are a plague to you, the user. But, to the people unleashing them, they’re quite beneficial and lucrative. That’s why more and more infections of the type pop up each day. The X3M ransomware is among the newest such threats. The infection is part of the ransomware family. It invades your system, and quite slyly so. Then, it locks your data, and extorts you for money. And, like with all ransomware, you face the same conundrum. To pay or not to pay. Let’s examine your options, shall we? If you pay, there are several scenarios that can go down. However, they all end badly for you. That’s because after payment, you rely on cyber criminals to keep their word. And, that’s a silly notion to say the least. Don’t be naive. These people WILL double-cross you. And, odd are, you’ll reach the same ending of the ‘no compliance’ option. In other words, you won’t get your data back. It remains locked. Only, if you don’t pay in the first place, you only lose your data. But if you pay, hoping for the best, you lose much more. You lose your money, your data, as well as your privacy. That’s right. Your privacy. By transferring the ransom amount, you provide your personal and financial details. Information, which can then get accessed by the cyber criminals, who are extorting you. Let that sink in for a moment. Extortionist strangers with malicious agendas get access to your private life. That will NOT end well for you. So, why not do yourself a favor, and pick the lesser evil? Forsake your files in the name of your privacy. It’s much more precious than pictures and videos.
How did I get infected with?
The X3M infection employs the same old tricks to invade your system. It resorts to the old but gold methods of infiltration. That includes hitching a ride with freeware or corrupted links. It can even pretend to be a fake update. Like, Java or Adobe Flash Player. But the most common means of invasion is via spam email attachments. That’s why you have to wary of emails from unknown senders. The infection often lurks behind seemingly legitimate ones. For example, one sent by Amazon or PayPal, urging you to open it ASAP! And, not just open the email. Oh, no. That won’t be enough to catch the cyber plague. It also requests you to download an attached document. It’s usually a contract or something else that seems important. But it’s not. That’s the ransomware in disguise! So, don’t fall for the deceit! It’s all lies! Look at every email you receive with a grain of salt. Especially, if it’s sent by a suspicious sender and contains attachments. Don’t trust everything you see online. If anything, go the opposite direction. Know that it’s always better to go the extra mile. Don’t rush, and don’t throw caution to the wind. Also, don’t forget to take the time to do your due diligence. Even a little extra attention can save you a ton of troubles.

Why is X3M dangerous?
The X3M infection is quite the hazard. It follows a pretty standard programming, with a few distinctions. Once the tool slithers into your system, it gets to work. It encrypts every single file you keep on your computer. Documents, pictures, music, videos, everything. It all falls under its clutches. The X3M tool locks your data by placing special attachments. It uses three particular ones. They are: .id-[random numbers]_locked, .id-[random numbers]_r9oj, and .id-[random numbers]_x3m. If you see your files with these extensions, that’s it. They’re locked. And, no amount of renaming or moving them will unlock them. The only way to free them of the infection’s grasp is with a decryption key. And, that key will cost you. After the program does what it’s designed to do, and encrypts everything, it displays a message. It’s the ransom note, and it contains explanations and instructions. You find it on your Desktop, as well as in each folder, harboring locked files. It requests you contact the cyber criminals via email. Either deyscriptors24@india.com, deyscriptors1@india.com, or server-support@india.com. Once you write them, they’ll respond with the address of a Bitcoin-wallet. You’re expected to transfer the ransom there. The exact amount is 0.8 Bitcoins. In case, you don’t know, 1 Bitcoin equals about $600. So, it’s no small sum. But, as was already explained, it’s not the ransom amount that should worry you. Even if it were $1, experts still advise against payment. You don’t want to open a door, you can’t close by transferring the ransom, do you? Keep the cyber criminals behind the X3M out of your private life! Do NOT comply with their demands! Discard your data for your privacy. It’s a tough decision to make, but it’s the wise one.
X3M Removal Instructions
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover X3M Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.
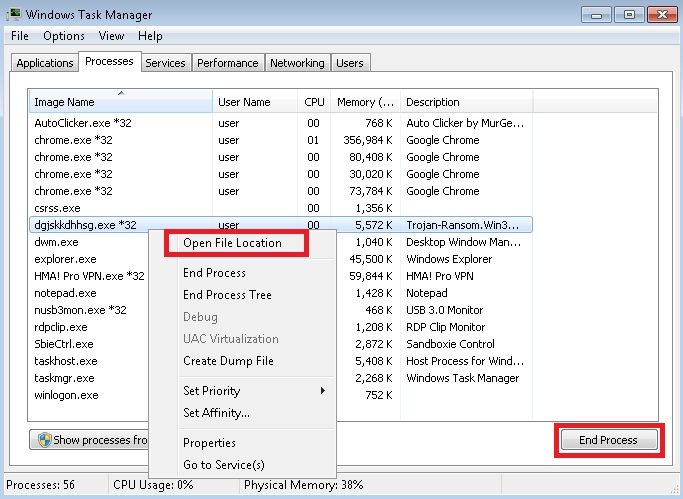
- Locate any suspicious processes associated with X3M encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate X3M encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]
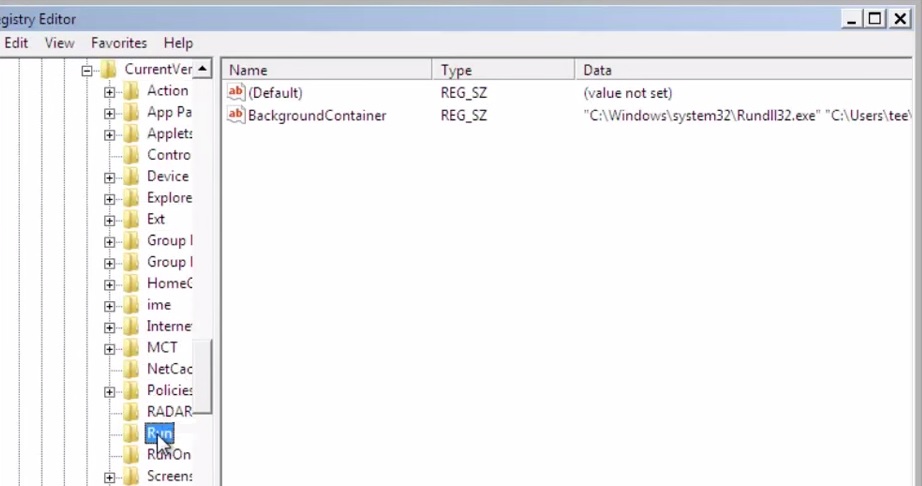
- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
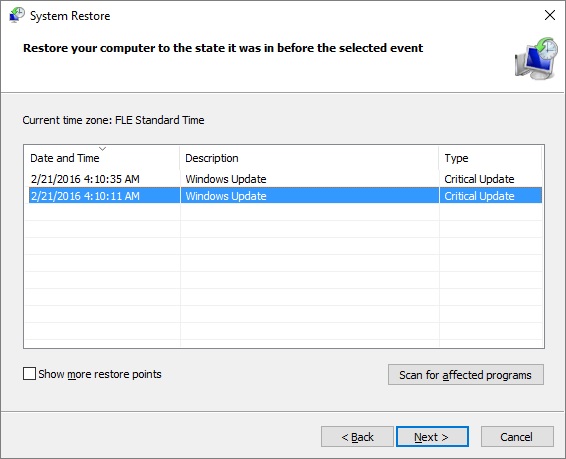
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.
- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.