Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Rumba Ransomware?
Readers recently started to report the following message being displayed when they boot their computer:
———————————————- ALL YOUR FILES ARE ENCRYPTED ———————————————–
Don’t worry, you can return all your files!
All your files documents, photos, databases and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://files.danwin1210.me/uploads/01-2019/Decrypt Software Overview.avi
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” folder if you don’t get answer more than 6 hours.
—————————————————————————————————————————
To get this software you need write on our e-mail:
pdfhelp@india.com
Reserve e-mail address to contact us:
pdfhelp@firemail.cc
Your personal ID:
Rumba is the name of a ransomware threat. It goes by that name, because that’s the extension you see, when it strikes. Let’s explain. As soon as Rumba infiltrates your system, its programming kicks in. The infection uses encryption algorithms to lock your files. It seizes control of all the files, you keep on your computer. Documents, archives, videos, music, pictures. All of it gets encrypted. To solidify its hold over it, the ransomware adds the extension. Say, you have a photo named ‘1.jpg.’ After Rumba’s done with it, it becomes ‘1.jpg.rumba.’ After that’s in place, you can no longer access your data. Moving or renaming them, does not help. The only way to release them from under the infection’s control is via compliance. The cyber threat makes sure you become aware of that through its note. Once it completes the encryption process, it leaves a ransom note on your Desktop. You can also find it in every folder that contains encrypted files. It’s a text file that contains pretty standard information. It explains your predicament, and provides a way to get out of thin. Comply and pay a ransom to the cyber kidnappers behind Rumba. They demand payment of 980 US Dollars. And, claim that buys you the decryption key, you need to free your files. Apply it, and your files get decrypted. That all seems fine and dandy, but is it an actual possibility? Ask yourself this. Can you trust the promises of cyber criminals that extort you for money? The answer is ‘No.’ So, don’t. Throwing money at the problem, won’t make it go away. Don’t lose your money, resting on the word of malicious strangers. They’ll break their word, and let you down. Do NOT reach out to these people, or pay them a single dime.
How did I get infected with?
The Rumba threat slithers its way in via the usual tricks. It turns to the old but gold invasive methods. Like, hiding behind freeware, as well as corrupted links and torrents. It can also pretend to be a fake system or program update. And, of course, it can use spam emails as a way in. Say, you receive an email that seems legitimate on the surface. Supposedly, it’s from Amazon, PayPal or some other well-known company. The contents urge you to click a link or download an attachment. It claims it’s something important, and hopes you fall for its trickery. Do NOT! Don’t give into carelessness. Carelessness leads you to act against your best interests. Don’t click or download anything in blind trust. Don’t allow anything into your system, without doing proper due diligence. Even a little extra attention can save you countless issues. Infections prey on your distraction, haste, and naivety. Don’t provide them. Choose caution over the lack thereof. It provides the far better alternative.

Why is Rumba dangerous?
After your data gets corrupted, and locked by Rumba, you have a decision to make. To comply or not. Experts urge against compliance. It guarantees you nothing. Well, nothing apart from losing your money. And, 980 US Dollars is no small amount. But, here’s the thing, even if the ransom were a single dollar, you’d still be advised against payment. Why? Well, the matter of guarantees remains. All you have to go on, is the promise of unknown individuals. People with malicious intentions. People you cannot rely on. Let’s examine your options, shall we? Say, you pay up. What then? You wait to receive the decryption key. But what if you don’t get it? Or, get one that doesn’t work? And, even if it does, you’re still not in the clear. Yes, you got rid of the encryption. But the encryptor remains. The key you pay for, doesn’t do anything about the ransomware. So, the Rumba threat remains, ready to strike once more. Nothing stops it from encrypting your files an hour after you’ve decrypted them. Then, you’re back to square one. It may seem harsh, but it’s not worth the risk. Payment ensures nothing but the loss of your money. Don’t pay.
Rumba Removal Instructions
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Rumba Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.
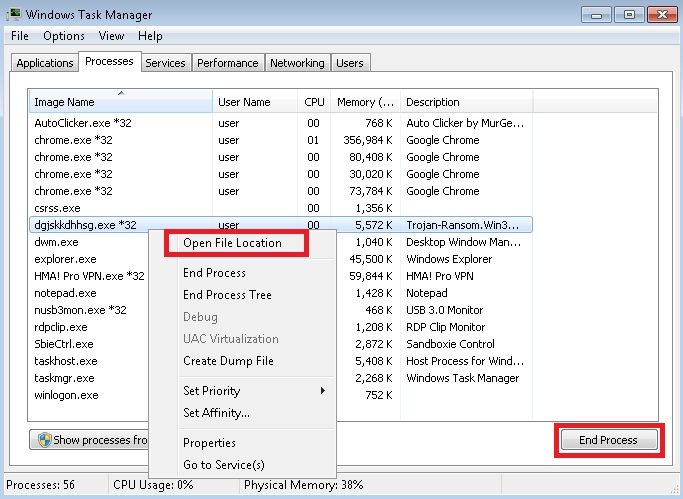
- Locate any suspicious processes associated with Rumba encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Rumba encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]
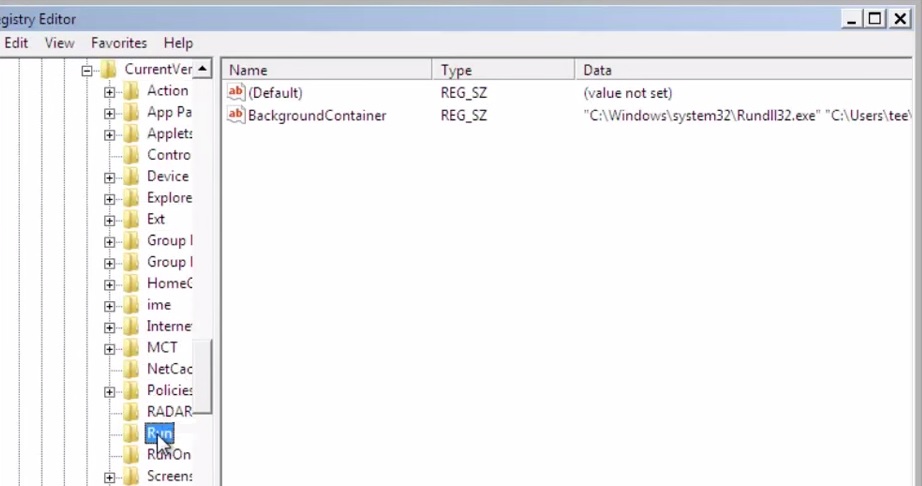
- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
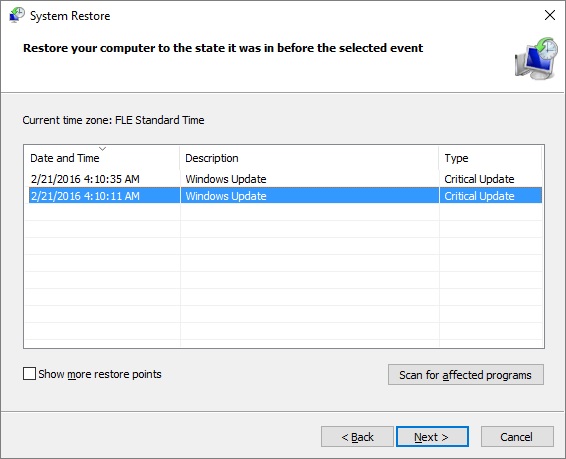
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.
- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.


